Step 1: Find the right Wi-Fi
So in our 99.99999% theoretical scenario, you and your laptop are within range of your neighbor’s Wi-Fi router. You don’t know the password, but you want to connect. Time to do some crimes.
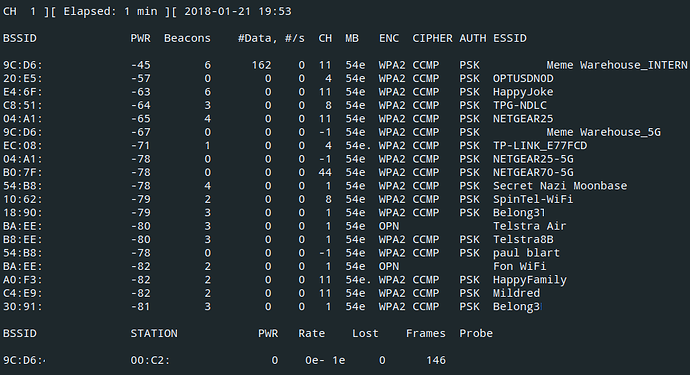
The first thing you’d do is take out your laptop and run airodump-ng, a tool for precisely the job of hacking Wi-Fi.
Here’s what it looks like:
BSSIDS
You see the names of nearby Wi-Fi networks and also their “BSSID”, which is a bit like an ID for Wi-Fi networks. It’s actually exactly like that.
Step 2: Get the password hash
Once you know the BSSID of your neighbor’s Wi-Fi, the goal is to get the Wi-Fi password. The router won’t tell you the Wi-Fi password, but it will give up the password hash1.
A password hash is like a scrambled version of the password. You can’t unscramble it. Kinda like how you can’t unscramble scrambled eggs back into the white and the yolk.
We’re going to find the hash by watching……the secret handshake.
The secret handshake
You heard me.
“is that real”
You might be wondering why there’s a secret handshake happening every time you connect to Wi-Fi, and that’s fair enough, I’m glad you asked.
Let’s say you’re a legitimate businessperson just connecting to your home Wi-Fi. No funny business. You know the password. But you need to prove to the Wi-Fi that you know the password. And the Wi-Fi needs to prove to you that it knows the password. The trouble is, everyone else can hear you.
Wi-Fi is broadcast as radio waves out of your device and router all the time. Anyone within range can hear what you’re saying.
It’s kinda like if you came up to me at a party and you said “I know your Facebook password”. It gets real tense. I nervously glance up at you and say “Really?”. I want to know if you really do know my Facebook password, but I also don’t want you to just say “Your Facebook password is cooldude69” because everyone else at the party is listening.
So, the secret handshake lets you and the Wi-Fi router both prove you know the password without saying it.
Eavesdropping
The trick is that by spying on the handshake, an eavesdropper (that’s us) could see:
- A randomly chosen bit of text (e.g. 3b5ef)
- The same text, encrypted with the Wi-Fi password as the key (b8%&G)
You know the text, you know what it encrypts to, and you know how to do the encryption. The only thing you don’t know is what the key is. This means that you can guess something as the key, and check if your guess was right.
We see “3b53f” encrypts to “b8%&G”
Try encrypting “3b53f” with key “password1” → “AAERJ” // Wrong!
Try encrypting “3b53f” with key “cooldad1964” → “b8%&G” // Found it!
What if you just encrypt the text 3b5ef with cooldad1964 as the key, and it happens to encrypt to b8%&G?
Then you know that the password was cooldad1964. And if 3b5ef encrypts to something else, then you know your guess was wrong.
Step 3: Crack the password
So using the trick above, we’re going to just guess the password. The trick is that we’re going to be able to guess passwords way faster than if we were just typing them into the “Enter the password for this Wi-Fi network” box.
So, get out your pen and paper and blow the dust off that compass and straightedge because it’s time to do some encryption.
Just kidding, we’re not going to use pen and paper you big bozo. We’re going to use a graphics card.
Graphics cards are the part inside a computer that lets the computer be able to play 3D games such as PLAYERUNKNOWN’S ALLCAPS Murder Paradise and Viva Piñata: Party Animals. They also happen to be really fast at encrypting stuff.
So we’re going to get a big list of millions of passwords, and try them all to try and guess the Wi-Fi password.
artisanal_passwords.txt
Alright so you know how websites get hacked?
Sometimes, the hackers release the passwords of everyone on the website at the time it got hacked. You may have heard of these as “data breaches”. Sites that got hacked recently and had passwords publicly exposed include LinkedIn, Adobe, and Myspace.
You, a person with an internet connection, can find these lists via Google. No dark web, no getting behind 7 proxies and insisting that your parents only call you by your “code name”, no nothing.
There are two kinds of home Wi-Fi networks: The kind that are called NETGEAR-7BDFC, which probably have randomly generated passwords, and the kind that are called Chris & Liz 2013, with passwords that are in these password lists.
I’m going to guess that your neighbor’s password is probably in one of the heaps big lists of passwords. But to find out which one it is, we’re going to have to encrypt 3b5ef (in this example) with every single password in the list as the encryption key2, and see if any of them match what we saw the Wi-Fi password encrypt to (b8%&G).
(If your neighbor has one of those randomly generated passwords, then you’re out of luck. JUST kidding click here for a fun time.)
Now that you’ve “acquired” these password lists, you gotta figure out which password is the Wi-Fi password.
Rapid-fire password guessing
Hashcat is software that can take a password list and a hash3 (“b8%&G”) and try to “unhash” it by comparing it to all the passwords in the list. To give you an estimate of how long this takes, my computer can check 10 million passwords in about 10 minutes. Specialised computers overflowing with graphics cards can do this in seconds.
You just plug the file containing the handshake that you got in Step 2 into hashcat, as well as your password lists.
hashcat
![]()
And that’s it. Hashcat will likely just spit out the password, and you can just type it in the Wi-Fi “Enter the password” box. The main part is furiously guessing millions of passwords until we find the right one.
Make it useful worth try.
 !
!