One of the more interesting features of Windows 10 version 1903, otherwise known as the May 2019 Update, is the Windows Sandbox. The Windows Sandbox is a Windows 10 virtual machine that can be quickly launched so you can test downloaded programs,browsers extensions, and suspect sites without risk of infecting your normal Windows operating system.
For those who are security conscious and do not want to deal with installing a dedicated virtual machine program like VirtualBox, Hyper-V, or VMWare, you can instead install Windows Sandbox for a very basic Windows 10 virtual machine.
While this feature brings terrific functionality to those who do not want to deal with a dedicated machine to test program, it could be improved, which we will discuss at the end of the article…
Before installing the Windows Sandbox, it is important to note that enabling the Sandbox will also enable Hyper-V, which makes it so VMWare and VirtualBox cannot run on the computer until it is uninstalled.
Installing the Windows Sandbox
Before you can install the Windows Sandbox, you first need to make sure your computer meets certain requirements. These are:
- Windows 10 Pro or Enterprise build 1903 or later. There are ways to get it installed on Windows 10 Home, but those require a little extra work, which will not be covered in this article.
- AMD64 architecture
- Virtualization capabilities enabled in BIOS
- At least 4GB of RAM (8GB recommended)
- At least 1 GB of free disk space (SSD recommended)
- At least 2 CPU cores (4 cores with hyperthreading recommended)
To install Windows Sandbox, simply follow these steps:
- Make sure you are using Windows 10 Pro or or Enterprise running version 1903 or later.
- Make sure CPU’s virtualization is enabled in the computer’s BIOS.
- Click the Start button and search for Windows Features . When it appears in the search results, click on the Turn Windows features on or off control panel result.
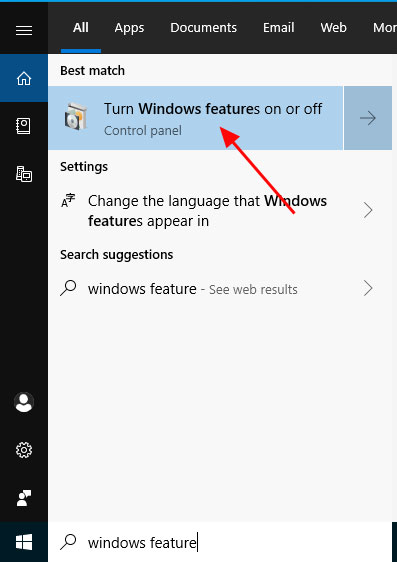
Open Windows Features Control Panel
- When the Windows Features control panel opens, scroll down and put a check in the box next to Windows Sandbox and then press the OK button.
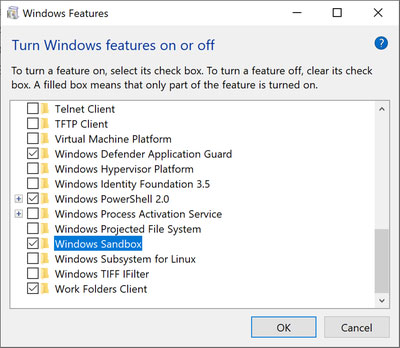
Add Windows Sandbox Feature
- After it has finished installing, Windows my ask you to reboot. Please allow it to do so.
The Windows Sandbox is now installed.
Using the Windows Sandbox
To use the Windows Sandbox, click on the Start button and search for Windows Sandbox . When it appears in the search results, click on it to launch the program.
When the Windows Sandbox loads for the first time, it may take a bit longer than normal as it generates the Windows 10 image it will use for the virtual machine. Once loaded, you will be presented with a Window that contains a fully functional base Windows 10 installation as shown below.
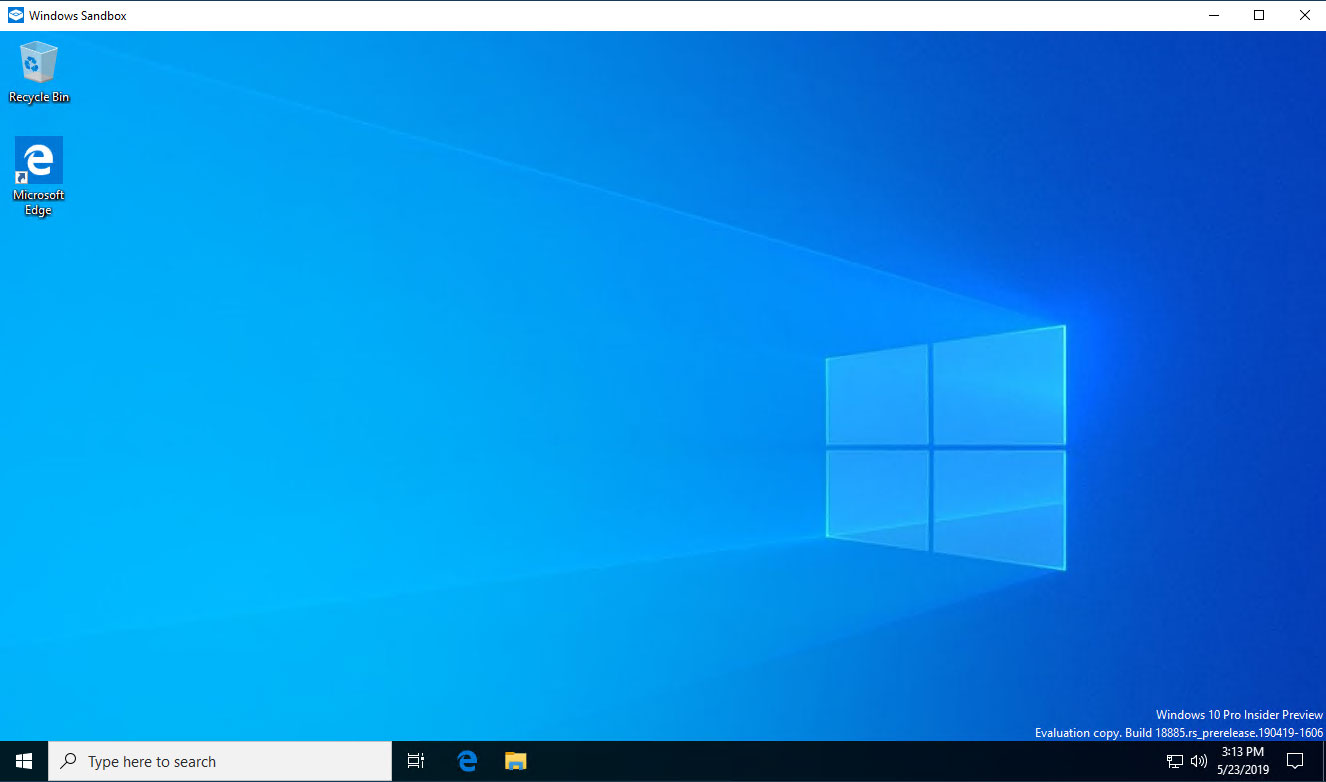
The Windows Sandbox
With the Windows Sandbox running, you can easily transfer files that you want to be tested or copy text to and from its clipboard. To transfer a file from your main Windows operating system (the Host), simply right-click on a file you want to transfer and select Copy .
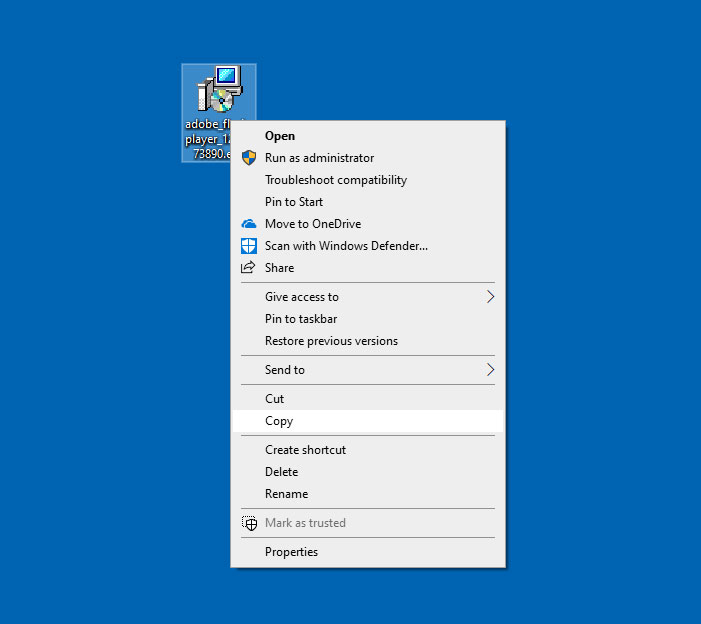
Copy file on the Host
Now, go in the Windows Sandbox (the Guest) and right-click on the desktop and click on Paste to transfer the file from your Host.
Transferring text between the Host machine and the Guest sandbox is easy as well, just copy text into the clipboard from either the main OS or the Sandbox and paste it into the other.
As an example of how the Windows Sandbox could be used, I just visited a site that stated I needed a Adobe Flash Player update. It looked a little fishy, so instead of running it on my main machine, I can fire up the Windows Sandbox and transfer the file there to test it.
I was lucky, because as you can see, this sure looks like an adware bundle rather than a Flash Player Update and is not something I would want to run on my normal computer. That’s because adware bundles have started to commonly install malware such as ransomware, miners, and password-stealing Trojans.
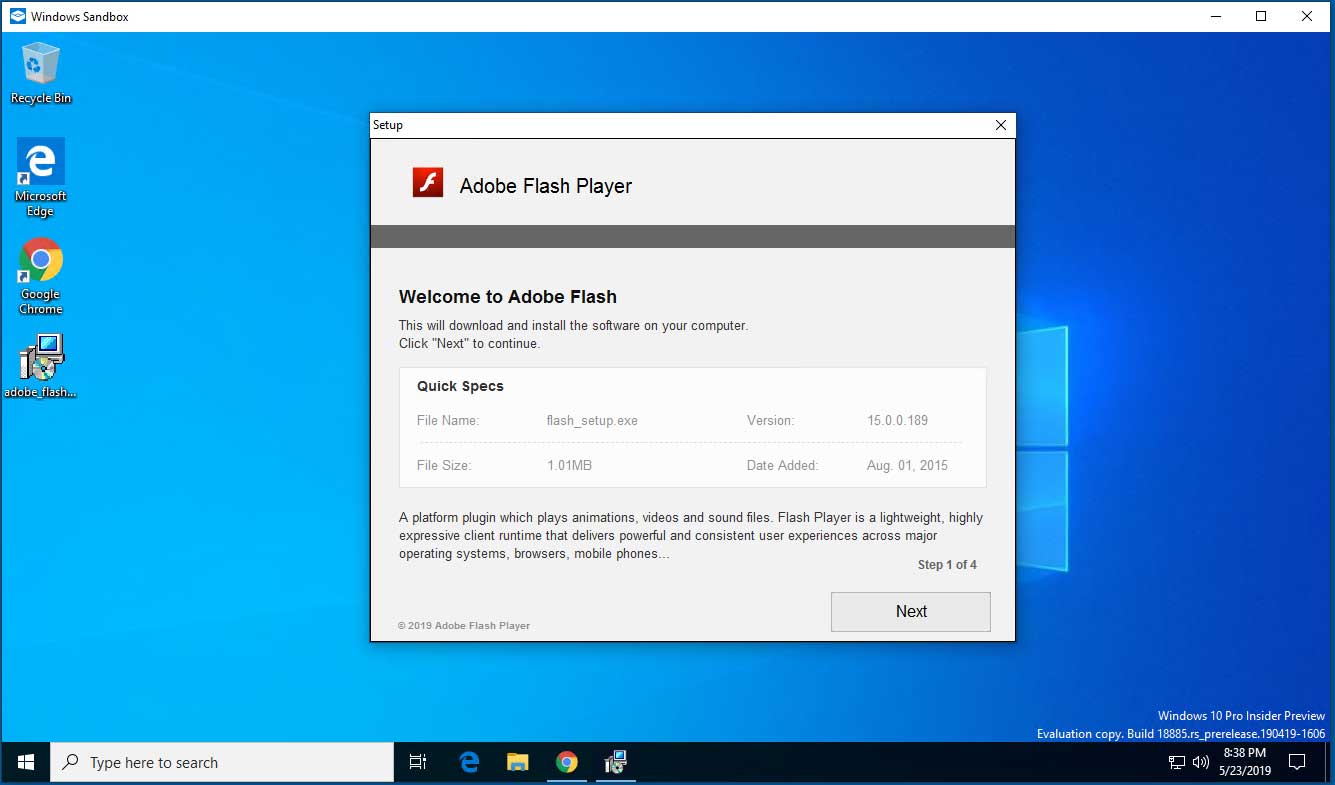
Windows Sandbox with Adware Bundle.
The good news is that anything you try out in the Windows Sandbox has no effect on your normal computer. So you can just try any program you download, malware or otherwise, or visit a web site and close the Sandbox when done with nothing to fear.
The next time you start it again, the Sandbox will be reset back to its default state so you can test more programs.
The Windows Sandbox is great, but could be better
Let me start out by saying I love the Windows Sandbox.
It is very easy to use, it allows users to quickly get a Windows 10 virtual machine up and running, and is accessible to users of all skill levels. This makes it very easy to test programs you download from the web or web browser extensions.
My only gripe is that it could be even better if we could easily use it to test malicious Office email attachments.
Malicious Word and Excel email attachments have become a very common method used to distribute malware such as ransomware, banking trojans, password-stealing Trojans, backdoors, downloaders, miners, and more.
Unfortunately, the Windows Sandbox only consists of a base operating system and no additional applications. This makes it impossible to test malicious Office documents such as Word and Excel documents without installing Office into the sandbox.
As the virtual machine is reset back to the default base image every time you close it, it can be a real pain if you want to use the Windows Sandbox to test email attachments.
It would be great if Microsoft included some way of testing malicious attachments. With that feature added, the Windows Sandbox would be incredibly useful for all users.
One other concern I have is that the Windows Sandbox can read the contents of your Host operating system’s clipboard. This means that if your Host has a password, or other sensitive information, saved to the clipboard, anything you run in the Sandbox will be able to access it.
To fix this, it would be nice if we had easy controls to control how clipboard data is transferred.
 !
!