In the era of data theft and everything remaining anonymous is very crucial. I have read a lot of ebooks online (paid as well as free) about remaining anonymous and hiding your identity online. All of the books lack something so not everyone is perfect. So I collected all of the information that I have learned from those ebooks and is sharing here completely free for our TechRim family. I know this post is going to be too long so I have decided to break the article in different parts. but read it through the end and you will get a pretty good idea about this.
1. Operating System
Protect Your Identity Online – Which OS shall you use
Many Guides online may suggest you to use Ubuntu to hide your identity online. That’s great in some extent too but with the newest additions of Ubuntu, they index and record your filesystem and searching habits to get few bucks out of you. So don’t shift to Ubuntu just because you want to remain anonymous.
My suggestion for you use -Debian -Linux Mint -Arch Linux -BSD, Which will help you protect your identity.
2. Encryption
Protect Your Identity Online – Encryption
Every site today is encrypted by HTTPS and vera crypt. Is it enough to protect your privacy online? I think you all have the answer to this and that is obviously a big “NO” . I have seen some people who are serious about their privacy using the GPG encryption 5096 bit RSA even while sending a message just to ensure that if their connection got sniffed, they never read the message.
My suggestions to you:
- Truecrypt your partitions, VHD’s, and other important files you need safe, always use a hidden partition with false files and such ….. IDK go to hack forums or torrent books about backtrack to make it look juicy yet dry.
- Use GPG for contacts here’s a nice link www.madboa.com/geek/gpg-quickstart/
- Encrypt your home folder when you install the OS of your choice
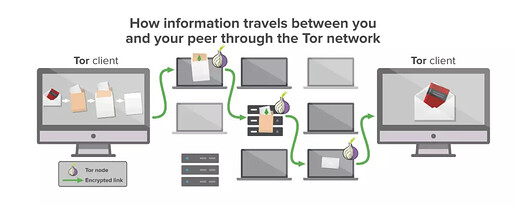
3. Tor / VPN
Protect Your Identity Online – TOR
Yeah, using VPN, Proxies or everything is great but don’t think that just using the VPNs will help you protect your identity. You have to do some work in yourself to protect your identity. Apart from using tor/ VPN what you should do is change the mac address every time you use your device.
For Linux follow the link to change the MAC Address.
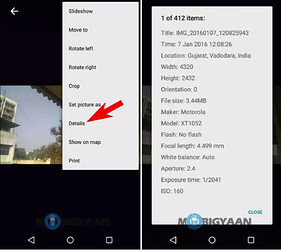
4. Do not upload a picture taken from your phone
Protect Your Identity Online – Encryption
Yeah, this sounds crazy but you should never upload the picture taken from the phone. I know sometimes I too upload the pictures taken from my phone but that the bad practice. You know why? Because while we capture the picture from our mobile phone the pictures embed with the GPS cord of where you took that picture. Plus there could be a feature within the picture itself that can give away who you are. I have read a couple of news about ATM hackers who got caught because of their silly mistake of uploading a picture from their phone.
Golden word of wisdom Always changes your DNS to Google DNS or Cloudflare DNS. Don’t use the DNS Provided by your ISP’s.
That’s the pretty much summary of how you can remain anonymous online. Hey, wait wait! That’s not enough to keep you 100% anonymous online. I will explain everything in detail to make sure you remain anonymous. Not only ISP’s but even government agents will be able to see what you are doing online.
If your privacy really matters for you then don’t quit reading here. Continue reading.
Actual post starts from here
I am currently using window vista and Mac, I am covering this article for window users for other OS, you may need to have someone fluent in that operating system to guide you through this process. However, most parts of the process are easily duplicated in another operating system.
In this guide from time to time, you will be instructed to go to certain URLs to download files. You do NOT need TOR to get these files, and using TOR (while possible) will make these downloads very slow. This guide may appear overwhelming. Every single step is explained thoroughly and it is just a matter of following along until you are done.
Once you are finished, you will have a very secure setup and it will be well worth the effort. Even though the guide appears huge, this whole process should take at the most a few hours. You can finish it in phases over the course of several days. It is highly recommended that you close ALL applications running on your computer before starting.
1 : Obtaining Tor Browser
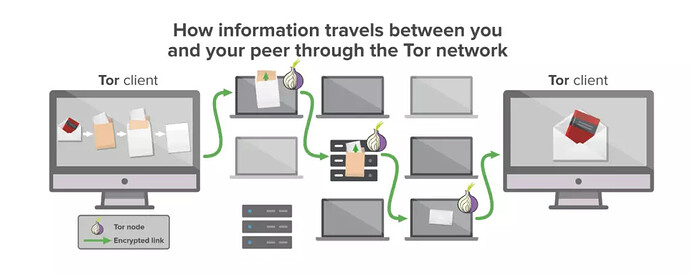
The first step to becoming secure and anonymous online is to set up and install something called “TOR”. “TOR” is short for” The Onion Router”. The concepts behind TOR were first implemented by the United States Military, and these principles have been used to create an extremely secure mechanism for being anonymous online. In fact, millions of people worldwide use TOR to browse the internet and communicate anonymously. TOR works by heavily encrypting your communications so that no observer can see what website you are really going to, and what information is really being sent. It all appears as a bunch of random characters to any observer. You simply use the TOR web browser just as you use any other web browser. TOR takes care of the rest.
However, TOR by itself is not enough. Even when using TOR, a user can be compromised in a number of ways. First, some websites can be set up to attempt to reveal someone’s true IP address (their true identity) by tricking their web browser or other software to transmitting that information. For this reason, anyone who uses TOR will recommend that no one have javascript or flash turned on while browsing TOR. In this guide, however, I will show you a much better solution. The second issue is that of human error.
Even if you have TOR installed, you may accidentally forget which browser to put in a link. You may also accidentally click on a link from another program, such as a chat program. That program might then load the link you clicked on into a non-TOR browser. When you are using TOR, you must be careful constantly that every link goes into the right browser and that you do not accidentally click the wrong link. So then, let’s begin. Obtaining the TOR Browser is easy. Simply go to the following website: http://www.torproject.org
Once here, you may feel free to read more about what TOR is and how it works, or you may proceed to immediately download TOR. Here is how it is done:
- Go to the website mentioned above and click on “Download TOR” or “Download”
- You will see text that says, “The Tor Browser Bundle contains everything you need … Just extract it and run. Learn more >>
- Click on this “Learn more” link. for the “Tor Browser Bundle”
- Assuming you are an English speaker, you would choose the top-most link “English (en-US)”. Otherwise, pick the language best suited to you.
- The file is saved will be named: tor-browser-1.3.18_en-US.exe
It is ok if the number is not exactly 1.3.18, there are new versions of Tor from time to time. - Run this file.
- You will be prompted to extract this to a directory.
By default, it will be set to C:\Users\You\Downloads
This is perfectly ok. You can also choose a different directory if you wish. - Click “Extract” That’s it. Tor Browser is NOW installed. Time to test it out!
2: Using and Testing Tor Browser for the first time
Now you have successfully downloaded and installed the Tor Web Browser Bundle. You are no doubt anxious to begin using it. First, click on the “start” menu icon, the icon in the lower-left of your screen with the windows logo. On the top right will be a listing that says “You”, “Documents”, “Pictures”, “Music”… “You” of course will be replaced by your user name.
Click on “You”, the top most link. This will open up your main user folder. Now, locate the folder called “Downloads” and double click on it. Now, inside the “Downloads” folder, double click on the folder called “Tor Browser”.
Lastly, double click on the application: “Start Tor Browser”
When you do, you will see the Vidalia Control Panel appear, and you will observe as you connect to the TOR network. When this is complete, your web browser will open up and will automatically connect to the web address: check.torproject.org This is to confirm that you are in fact using TOR.
If you have followed this guide correctly, then you will see the following green text, or something similar: “Congratulations. Your browser is configured to use Tor.” Now you can use this web browser the same as any other. You can go to any website you wish, and neither your ISP or anyone else will be able to see where you are going, or what you are doing. However, there are still issues that need to be resolved, so don’t begin browsing just yet.
IMPORTANT SAFETY NOTE:
If you fill out a form containing your email address, your name, or any other sensitive information while using the TOR browser, be aware that sometimes it is possible for an observer to see that information. When using TOR, use it to access websites and content that you are not connected to via your real identity or any username or nickname which links to your real identity. Let TOR be for anonymous browsing solely. Do your online banking, or any other activities involving your real identity using your normal web browser
3. Securing your Hard Drive
Being able to browse anonymously is one thing. However, you may choose to download and save sensitive content or material to your computer which you wish to keep private. This may include reading sensitive documents, viewing pictures, or storing any kind of sensitive data. If you save anything to your computer’s hard drive, then it is possible for someone who has confiscated your computer to determine what it was you saved. This is often true even if you delete the content.
For example, suppose I use the Tor Browser and I navigate to a website containing a sensitive document that I wish to read. If I saved that document somewhere on my hard drive, then it is possible for someone else to find it. If I delete that document, it may still be possible for someone to undelete it. Further, even if I never save it to my hard drive but I simply look at it using my word processing software, it may still be saved in a number of ways including:
- Often programs keep records of filenames. The filename alone is often enough to incriminate someone.
- Often programs keep parts of the content viewed saved for various reasons, such as for searching. This can include random excerpts of text, thumbnails of images, and more. Often this “partial” data is more than enough to prove what the original data was. Often the “partial” data is itself incriminating.
- Sometimes, especially if you are running low on system memory, your operating system may choose to use your hard-disk as a temporary RAM. This is known as “SWAP”. Normally, whenever you turn off your computer, whatever was in RAM is deleted. However, the data that goes to your SWAP may persist and it may be possible for someone to see what content you had open in your programs if that information is saved in RAM. Generally speaking, you must have a plan to secure any content that is saved to your hard disk. Therefore, this guide would be incomplete if we did not thoroughly address this.
First, there are two kinds of such content:
Deliberately saved content
Deliberately saved content refers to content that you have chosen to save on your hard disk so that you can access this content later. We will address how to do this later in the guide.
Inadvertently saved content
Inadvertently saved content refers to content that is saved by programs you use, or your operating system. You have no way to even know what this content might be. Therefore, this is the most dangerous. You may browse and find a dozen sensitive documents, utterly delete them, and some program may have saved the file names and excerpts of the data. This will render your previous efforts futile.
Content that is inadvertently saved to your harddisk comes in two flavors:
- Content that is saved to your SWAP space.
- Content that is saved by applications running on your computer, including your operating system.
The surest way to prevent content from writing to your SWAP space is to disable your SWAP space altogether. This may result in your computer running a bit slower than normal and may mean that you cannot use ram intensive games and applications during the time your SWAP is disabled. Therefore, if you use this method, simply turn back on the SWAP when you want to use those ram intensive applications. Also, you may choose not to take this step. Here is how to disable your swap space if you are using Windows 7:
ADVANCED INSTRUCTIONS BELOW. SKIP THIS IF YOU ARE NOVICE OR UNCOMFORTABLE WITH THIS OPERATION
This step is recommended for advanced users only. If you are not comfortable doing this, you may safely skip this step.
Instructions are less verbose than usual, as these steps are intended for advanced users only. If you do not fully understand these instructions, skip this step.
- From Control Panel, go to “System and Security”.
- Click on “System”, and then choose “Advanced system settings” in the left-most menu.
- Under the “Advanced” tab, under “Performance”, click “Settings”.
- Under this “Advanced” tab, under “Virtual Memory”, click “Change”
- Uncheck “Automatically manage paging file sizes for all drives”
- Select “No paging file”
- Save, reboot, and follow these same first 5 steps to confirm that “No paging file” is still selected
This means that you have successfully disabled your swap. This means that nothing from RAM will be inadvertently saved to your hard drive. To resume using SWAP again, simply click “Automatically manage paging file size for all drives.” You can switch between these two modes as you desire. Generally speaking, your computer will run fine without a swap file, provided you have enough RAM.
***** END OF ADVANCED INSTRUCTIONS *****
The next issue we need to address is how to prevent applications and/or your operating system from saving content inadvertently that you do not want to be saved. For this, we are going to set up a “Virtual Machine”.
A “Virtual Machine” is like a computer inside of your computer. Everything you do inside the Virtual Machine (VM for short) will be fully contained within itself and no one will be able to see what the VM has been doing. Ideally, you want ALL of your sensitive computer usage of any kind, TOR or NON-TOR, to take place within a VM. In this way, you can keep everything private that you wish while still using your computer fully and getting the most out of it. Don’t be afraid of this sounds complicated. This guide will take you through every step slowly and methodically. Before we can set up a VM however, we need to take another step.
That’s all for 1st part of the article, I will look forward to part 2 if something above required to get published. I hope you are getting idea about being anonymous in this virtual era. After the end of this whole part, I am assuring you that not even government agencies are going to trace you.
THESE PICTURES TAKEN FROM THE WEB, AND USED TO USE FOR EDUCATIONAL PURPOSES.

 !
!