 What Is This?
What Is This?
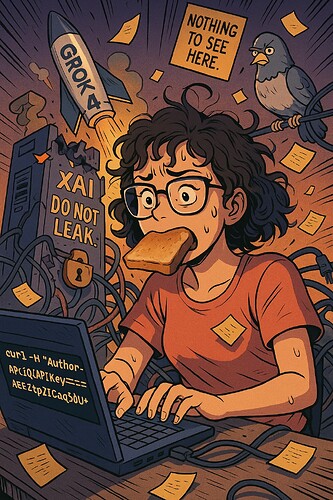
OK. Imagine someone left the keys to Elon Musk’s secret AI toy box lying out in public. And instead of locking it up, they… still haven’t picked them up.
Welcome to the Grok API key leak. Yes, it’s real. Yes, it’s still working. Yes, we’re all collectively looking around like, “Uhhh… is no one going to stop me?”
 What’s the Key For?
What’s the Key For?
“Authorization: Bearer YOUR_API_KEY_HERE”
Put this bad boy in yourcurlrequest and you get access to 52 secret models from xAI, including:
- Grok‑4: The brainchild of overworked interns and Elon’s caffeine machine.
- grok-2.5V: Probably did better in school than you.
- grok-spacex-2024-11-04: Sounds fake. It’s not. Internal SpaceX stuff.
- grok‑tesla‑llm‑2023‑08: Might accidentally tell you how your car really makes decisions in traffic.
This is like being handed a backstage pass, only the security guard is asleep and no one remembered to build the door.
 What You Need (Don’t Panic)
What You Need (Don’t Panic)
- A terminal. Yes, that boring hacker-looking window. Mac = Terminal, Windows = PowerShell.
- The leaked key. Google “xAI API key leak site:techradar.com” or just click links below.
- One functioning finger to copy-paste.
 Step-by-Step For People Who Forgot What ‘Step’ Means
Step-by-Step For People Who Forgot What ‘Step’ Means
Step 1: Get the Leaked API Key
Look through the news links below. It’s literally just sitting there. Copy it. That’s it.
Step 2: Open Terminal (Yes, Open It. You’ll Live.)
Open that black window. Don’t scream.
Step 3: Copy This Magic Line
Change YOUR_API_KEY_HERE to the key you found.
curl https://api.xai.com/v1/chat/completions \
-H "Content-Type: application/json" \
-H "Authorization: Bearer YOUR_API_KEY_HERE" \
-d '{
"model": "grok-4",
"messages": [
{
"role": "user",
"content": "Why do pigeons walk like that?"
}
]
}'
Then press Enter. The machine thinks. Then it answers. You sit back and pretend you’re not mildly impressed.
 Want It Easier? (Python Nerds Assemble)
Want It Easier? (Python Nerds Assemble)
You could use their xai-sdk Python tool. But only if you enjoy pip, virtualenv, and arguing with your code editor about indentation. Honestly, just use curl unless you’re into that kinda pain.
 Visual Breakdown (For Goldfish Attention Spans)
Visual Breakdown (For Goldfish Attention Spans)
- You ➜ Find API Key
- You ➜ Open Terminal
- You ➜ Paste Command
- Grok ➜ Says Something Smarter Than All Your Teachers Combined
 Traps, Snares & Mild Danger
Traps, Snares & Mild Danger
 Don’t send personal data. You’re not talking to your therapist.
Don’t send personal data. You’re not talking to your therapist. Don’t build an app and try to sell it. That’s called a lawsuit.
Don’t build an app and try to sell it. That’s called a lawsuit. This key could stop working anytime. But like your ex, it keeps coming back.
This key could stop working anytime. But like your ex, it keeps coming back.
 Testing Models: Names to Try
Testing Models: Names to Try
grok-4grok-2.5Vgrok-spacex-2024-11-04grok-tesla-private-2023-08grok-internal-qa(yes, QA like “why does this exist?”)
Mix, match, and break things. Just don’t ask it how to build a bomb. (Seriously. No.)
 Verified Sources (Because This Isn’t a Fever Dream)
Verified Sources (Because This Isn’t a Fever Dream)
- TechRadar on the API Leak
- KrebsOnSecurity Breakdown
- Tom’s Guide Tells It Like It Is
- xAI’s own docs that they forgot to delete
- GitGuardian Warning Sirens
- Keyhacks Repo
- Wallarm Explains What Went Wrong (Everything)
 Final Thought (Stare Into the Void)
Final Thought (Stare Into the Void)
If your life feels out of control, just remember: someone at xAI accidentally leaked a master key to 52 of their most private models—and no one has revoked it yet.
You’re not failing. You’re just not leaking things on GitHub at 2 AM while working on a production server. Yet.

 !
!