This framework is the end product of my experience in reverse engineering iOS kernelcache,I do manually look for vulnerabilities in the kernel and have automated most of the things I really wanted to see in Ghidra to speed up the process of reversing, and this proven to be effective and saves a lot of time. The framework works on iOS 12/13/14 and has been made to the public with the intention to help people to start VR in iOS kernel without the struggle of preparing their own environment, as I believe, this framework ( including the toolset it provides and with some basic knowledge in IOKit) is sufficient to start dealing with the Kernelcache.
The whole framework is written in Python,and can be extended to build tools upon, it provides some basic APIs which you can use in almost any project and save time from reading the verbose manual, you can just read the code in utils/ directory.
Ghidra is good when it comes to analyzing the kernelcache, but like other RE tools, it needs some manual work, ghidra_kernelcache provides a good entry point to fix things at the start and even while doing reverse engineering thus providing a good-looking decompiler output.
There is a similar project done by @_bazad in IDAPro called ida_kernelcache which provides a good entry point for researchers wanting to work with the kernel image in IDA, my framework looks a bit similar to Brandon’s work, and goes beyond by providing much more features to make the process of working with the kernelcache a lot easier.
Here are some of the features provided by the framework :
- iOS kernelcache symbolication.
- Resolving virtual call references.
- Auto fixing external method array for both
::externalMethod()and::getTargetAndMethodForIndex(). - Applying namespaces to class methods.
- Symbol name and type propagation over function arguments.
- Applying function signatures for known kernel functions.
- Import old structures and classes from old project to a new project.
- Auto type-casting
safeMetacast()return value to the appropriate class object type.
These features are made as a separated tools which can be executed either by key shortcuts or by clicking on their icons in the toolbar.
Installation
Clone the repository :
git clone https://github.com/0x36/ghidra_kernelcache.git $APATH
Go to Windows → Script Manager, click on script Directory , then add $APATH/ghidra_kernelcache to the directory path list.
Go to Windows → Script Manager, in scripts listing, go to iOS→kernel category and check the plugins seen there, they will appear in GHIDRA Toolbar .
in logos/ directory, you can put you own logos for each tool.
iOS kernelcache symbolication
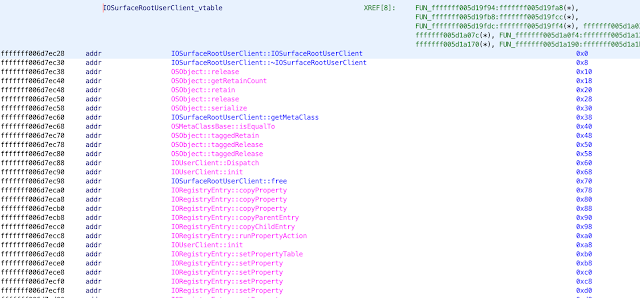
ghidra_kernelcache requires at the first stage iometa (made by @s1guza), a powerful tool providing C++ class information in the kernel binary, the great thing is that it works as a standalone binary, so the output can be imported to your favorite RE framework by just parsing it. My framework takes iometa’s output and parses it to symbolicate and fix virtual tables.
Usage
After decompressing the kernel, run the following command :
$ iometa -n -A /tmp/kernel A10-legacy.txt > /tmp/kernel.txt# if you want also to symbolicate using jtool2$ jtool2 --analyze /tmp/kernel
Load the kernelcache in Ghidra, DO NOT USE BATCH import , load it as Mach-O image. After the Kernelcache being loaded and auto-analyzed, click on the icon shown in the toolbar or just press Meta-Shift-K, then put the full path of iometa output which is /tmp/kernel.txt in our case.
if you want to use jtool2 symbols, you can run jsymbol.py located iOS→kernel category as well.
Using APIs
Full API examples are in ghidra_kernelcache/kc.py
→ Here are some examples of manipulating class objects :
Continue following: