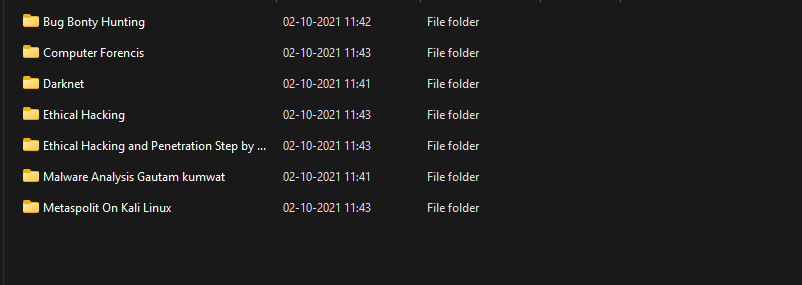
- Bug Bonty Hunting
- Computer Forensics
- Darknet
- Ethical Hacking and Penetration Step by Step with Kali Linux
- Ethical Hacking
- Malware Analysis
- Metaspolit On Kali Linux
Happy learning!
DISCLAIMER: No Copyright Infringement Intended, All Rights Reserved to the Actual Owner.
This content has been shared under Educational And Non-Profit Purposes Only.
 !
!