CYBERONIX












Description
Cyberonix is an open-source and free tool developed by Team Defronix Cyber Security Pvt. Ltd. Initially created by a team of students during their internship at Defronix after completing their Diploma in Cyber Security Training.
This tool serves as a comprehensive resource hub for the Cyber Security Community. Our objective is to establish it as a one-stop solution for hackers, providing resources on various topics within Cyber Security. We are committed to regularly updating the tool and incorporating new and relevant resources.
Please feel free to suggest any features you would like to see in this tool, we welcome your input and will be delighted to include suggested features in our upcoming updates.
Install
Usage
Categories
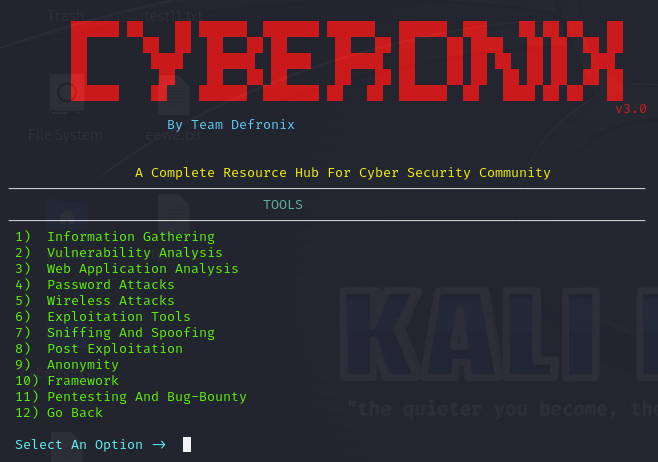
ScreenShots
Contributors
Installation
- Update your system packages:
sudo apt update -y && apt full-upgrade -y
- Clone the Cyberonix repository from GitHub:
git clone https://github.com/TeamDefronix/Cyberonix.git
- Navigate to the Cyberonix directory:
cd Cyberonix
- Make the setup script executable:
chmod +x setup.py
- Run the setup script using Python3:
sudo python3 setup.py
- Execute Cyberonix:
cyberonix
PIP intallation
pip install cyberonix
If you encounter the “Externally-Managed-Environment” issue on your machine, please refer to our blog for a solution. You can find detailed information and steps to resolve this problem by clicking here.
Usage
- To display the help menu, use the following command:
cyberonix -h
- To exit the Cyberonix tool, press:
ctrl+c
- Press the
enter key to navigate back.
Below are the instructions to access the tool’s help function, along with a complete list of all available switches:
Welcome to Cyberonix - Your Cyber Security Resource Hub! Basic Options: -h, --help : Get this help message. --domain DOMAIN, -D DOMAIN : Target a specific domain. --output OUTPUT, -o OUTPUT : Save results to a file (provide the file path). --file FILE, -f FILE : Read input from a file (provide the file path). --ip IP, -ip IP : Target a specific IP address. Main Functions: --tools, -t : Access various cybersecurity tools. --cheatsheet, -c : Get a cybersecurity reference guide. IP Operations: --getip, -gip : Get the IP address of a domain. Can use with: --domain, --file, --output --ipinfo, -ipi : Get information about an IP address. Can use with: --ip, --file, --output DNS Operations: --dnsrecord, -dns : Get DNS records for a domain. Can use with: --domain, --file, --output --record RECORD, -r RECORD : Specify the type of DNS record (e.g., A, TXT, MX). usage: --record ASN Record: --asnrecord, -asn : Get ASN (network) information. Can use with: --ip, --file, --output Screenshoting: --screenshot, -s : Take a website screenshot. Can use with: --domain, --file, --output HTTP Status: --http-status, -S : Check a website’s HTTP status code. Can use with: --domain, --file, --output Remove Duplicate: --remove-duplicate, -rd : Remove duplicate lines from a file. Can use with: --file, --output Password Generation: --passwordgen, -P : Generate a secure password. --default-password-gen, -pass: Generate a strong random password (recommended). Customization Options: --upper, -u : Include uppercase letters. --lower, -l : Include lowercase letters. --digits, -d : Include numbers. --punctuation, -p : Include symbols. --length LENGTH, -L LENGTH : Set password length (default is 8). --checkpassword, -C : Test the strength of a password. Worlist Generation: --worlist, -w : To generate a wordlist --characters,-c : Set of characters to include in the wordlist (Default = abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789 ) --min_length, -min : Minimum length of the words ( Default = 4 ) --max_length, -max : Maximum length of the words ( Default = 6 ) --output_file, -ot : Output file name ( Default = custom_wordlist.txt )
Categories
Information Gathering
| Tool Name |
Tool Name |
Tool Name |
| Useful Websites |
Nmap |
Subfinder |
| Maltego |
Dracnmap |
Red_Hawk |
| Th3Inspector |
Hping3 |
Arping |
| Netdiscover |
The Harvester |
Wafw00f |
| Recon-Ng |
Sublist3R |
Spiderfoot |
| Amass |
|
|
Vulnerability Analysis
| Tool Name |
Tool Name |
Tool Name |
| Wpscan |
Wireshark |
Wapiti |
| Nmap |
Legion |
Nikto |
| Wfuzz |
|
|
Web Application Analysis
| Tool Name |
Tool Name |
Tool Name |
| Burp Suite |
Dirsearch |
Owasp Zap |
| Dirbuster |
Nikto |
Wapiti |
| Nessus |
Dirb |
Nuclei |
| Ffuf |
|
|
Password Attacks
Brute Force Attacks
| Tool Name |
Tool Name |
Tool Name |
| Hashcat |
John The Ripper |
Hydra |
| Johnny (GUI John) |
Brutus |
Dirbuster |
| Reaver |
Dirsearch |
|
Dicitionary Attacks
| Tool Name |
Tool Name |
Tool Name |
| Hashcat |
John The Ripper |
Hydra |
| Medusa |
Ncrack |
Johnny (GUI John) |
Rainbow Table Attacks
| Tool Name |
Tool Name |
| Rainbowcrack |
Ophcrack |
Wordlist Generator
| Tool Name |
Tool Name |
Tool Name |
| Crunch |
Cupp |
Bopscrk |
Phishing Attacks
| Tool Name |
Tool Name |
Tool Name |
| Social-Engineer Toolkit (SET) |
Hiddeneye |
R3Bu5 |
| Zphisher |
Shellphish |
Gophish (GUI) |
| Camphish |
|
|
Keylogger Attacks
| Tool Name |
Tool Name |
| Zlogger |
Keylogger |
Wireless Attacks
| Tool Name |
Tool Name |
Tool Name |
| Kismet |
Wifite |
Fern Wifi Cracker |
| Aircrack-Ng |
Fluxion |
Wifiphisher |
Exploitation Tools
| Tool Name |
Tool Name |
Tool Name |
| Metasploit |
Crackmapexec |
Searchsploit |
| Beef |
Routersploit |
Sqlmap |
| Seclists |
Airmitage |
|
Sniffing And Spoofing
| Tool Name |
Tool Name |
Tool Name |
| Wireshark |
Bettercap |
Tcpdump |
| Arpspoof |
Dsniff |
Scapy |
| Netsniff-Ng |
Macchanger |
Responder |
| Airgeddon |
Sharesniffer |
Wifi-Pumpkin-3 |
| Mitmproxy |
Zaproxy |
|
Post Exploitation
| Tool Name |
Tool Name |
Tool Name |
| Metasploit-Framework |
Linpeas |
Linenum |
| Sudo Killer |
Beroot |
Linux Exploit Suggester 2 |
| LSE (Linux Smart Enumeration) |
Pspy |
Bashark |
| Linux Private-I |
Shellter |
Amber |
| Upx (Ultimate Packer for Executable) |
Covermyass |
|
Anonymity
| Tool Name |
Tool Name |
Tool Name |
| Tor |
Anonsurf |
Nipe |
| Proxychain |
|
|
Framework
| Tool Name |
Tool Name |
| OSINT Framework |
MITRE Framework |
Pentesting And Bug-Bounty
Information Gathering
| Tool Name |
Tool Name |
Tool Name |
| Useful Websites |
Nmap |
Subfinder |
| Maltego |
Dracnmap |
Red_Hawk |
| Th3Inspector |
Hping3 |
Arping |
| Netdiscover |
The Harvester |
Wafw00f |
| Recon-Ng |
Sublist3R |
Spiderfoot |
| Amass |
|
|
Configuration Management
| Tool Name |
Tool Name |
Tool Name |
| Dirb |
gobuster |
Nikto |
| Wfuzz |
Skipfish |
Dirbuster |
| Feroxbuster |
Nmap |
Httpie |
| Metasploit |
Securityheaders |
Sqlmap |
| Trufflehog |
Gitleaks |
Secretfinder |
Secure Transmission
| Writeups |
Writeups |
| Check SSL Version, Algorithms, Key Length |
Check for Digital Certificate Validity |
| Check Credentials Only Delivered Over HTTPS |
Check Session Tokens Only Delivered Over HTTPS |
| Check if HTTP Strict Transport Security (HSTS) |
|
Authentication
| Writeups |
Writeups |
Writeups |
| User Enumeration |
Authentication Bypass |
Vulnerable Remember Me Functionality |
| Password Reset |
Captcha Bypass |
Autocomplete On |
| Multifactor Authentication |
Logout Functionality |
Cache Management |
| Default Credentials |
|
|
Session Management
| Tool Name |
Tool Name |
Tool Name |
| OWASP Zap |
BurpSuite |
Nikto |
| Nmap |
Wapiti |
Nessus |
| Nuclei |
Fiddler |
Penetration Testers Framework (PTF) |
Authorization
| Tool Name |
Tool Name |
Tool Name |
| BurpSuite |
Wireshark |
OWASP Zap |
| Nessus |
Hydra |
Beef |
| Sqlmap |
Metasploit |
Nmap |
| Penetration Testers Framework (PTF) |
|
|
Data Validation
| Tool Name |
Tool Name |
Tool Name |
| XSS |
XXE - XML |
HTML Injection |
| SQL Injection |
Command Injection |
HTTP Smuggling |
| HTTP Parameter Pollution |
Open Redirection |
LFI |
Denial Of Service
| Tool Name |
Tool Name |
| Goldeneye |
Slowhttptest |
| Thc-SSL-Dos |
Slowloris |
Business Logic
| Writeups |
Writeups |
| Business Logic |
Exploiting Business Logic Vulnerabilities |
| Web Application — Business Logic Vulnerabilities |
Business Logic Flaw |
Cryptography
| Tool Name |
Tool Name |
Tool Name |
| SSLstrip |
Bettercap |
Ettercap |
| SSLyze |
0-Saft |
SSLscan |
| SSLLabs |
|
|
Risky Functionality - File Uploads
| Tool Name |
Tool Name |
| Fuxploider |
Upload Scanner |
Risky Functionality - Card Payment
| Tool Name |
Tool Name |
Tool Name |
| BurpSuite |
Wireshark |
OWASP Zap |
| Nessus |
SQLmap |
Fiddler |
| Metasploit |
Nmap |
Penetration Testers Framework (PTF) |
Html 5
| Writeups |
Writeups |
Writeups |
| Web Messaging |
Web Storage SQL Injection |
CORS Implementation |
-
Cheatsheets
-
Certifications & Roadmap
-
Beginner Level Certifications
-
Advance Level Certifications
-
Bug Bounty
- Bug Bounty for Beginners
- Reconnaissance
- Intel Discovery
- Enumeration
- Vulnerability Analysis
- Exploitation
- Reporting
Screenshots




GitHub:

 !
!