C2 Tracker
Free to use IOC feed for various tools/malware. It started out for just C2 tools but has morphed into tracking infostealers and botnets as well. It uses Shodan searches to collect the IPs. The most recent collection is always stored in data; the IPs are broken down by tool and there is an all.txt.
The feed should update daily. Actively working on making the backend more reliable
Honorable Mentions
Many of the Shodan queries have been sourced from other CTI researchers:
Huge shoutout to them!
Thanks to BertJanCyber for creating the KQL query for ingesting this feed
And finally, thanks to Y_nexro for creating C2Live in order to visualize the data
What do I track?
- C2’s
- Malware
- AcidRain Stealer
- Misha Stealer (AKA Grand Misha)
- Patriot Stealer
- RAXNET Bitcoin Stealer
- Titan Stealer
- Collector Stealer
- Mystic Stealer
- Gotham Stealer
- Meduza Stealer
- Quasar RAT
- ShadowPad
- AsyncRAT
- DcRat
- BitRAT
- DarkComet Trojan
- XtremeRAT Trojan
- NanoCore RAT Trojan
- Gh0st RAT Trojan
- DarkTrack RAT Trojan
- njRAT Trojan
- Remcos Pro RAT Trojan
- Poison Ivy Trojan
- Orcus RAT Trojan
- ZeroAccess Trojan
- HOOKBOT Trojan
- Tools
- Botnets
Running Locally
If you want to host a private version, put your Shodan API key in an environment variable called SHODAN_API_KEY
echo SHODAN_API_KEY=API_KEY >> ~/.bashrc bash python3 -m pip install -r requirements.txt python3 tracker.py
Contributing
I encourage opening an issue/PR if you know of any additional Shodan searches for identifying adversary infrastructure. I will not set any hard guidelines around what can be submitted, just know, fidelity is paramount (high true/false positive ratio is the focus).
References
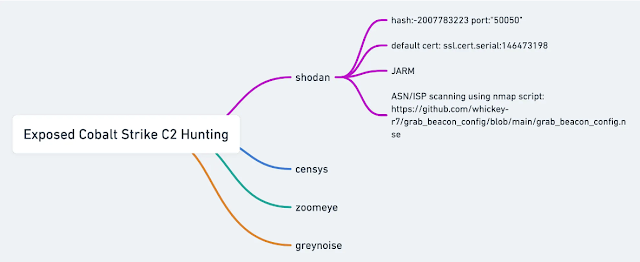
- Hunting C2 with Shodan by Michael Koczwara
- Hunting Cobalt Strike C2 with Shodan by Michael Koczwara
- https://twitter.com/MichalKoczwara/status/1591750513238118401?cxt=HHwWgsDUiZGqhJcsAAAA
- BushidoToken’s OSINT-SearchOperators
- https://twitter.com/MichalKoczwara/status/1641119242618650653
- https://twitter.com/MichalKoczwara/status/1641676761283850241
- https://twitter.com/_montysecurity/status/1643164749599834112
- https://twitter.com/ViriBack/status/1713714868564394336
- https://gi7w0rm.medium.com/the-curious-case-of-the-7777-botnet-86e3464c3ffd
- https://twitter.com/Glacius_/status/1731699013873799209
 !
!