Today I’m gonna share another interesting finding which is a password reset vulnerability without user interaction.
Earned $1,200 ![]()
Basically, the vulnerability allows me to reset the password of any user if I know the username of the victim and luckily the target application was also vulnerable to user enumeration vulnerability.
Vulnerability Explanation:
These type of vulnerabilities occurs when a server does not validate the inputs properly, Input validation is one of the most important and necessary security control.
So without wasting more time let’s start……
I was testing a private Bug Bounty Program on HackerOne, I was looking for user enumeration first.
Forgot password panel is the best place to enumerate the registered users of an application, I enumerate the user from forgot password after that I observe the target application has some different mechanism to reset the password.
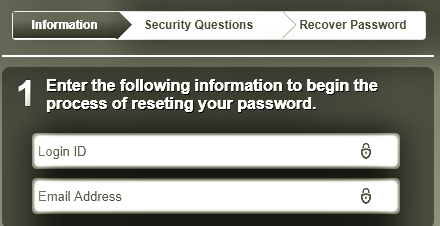
Means it take the username, email, and security questions and then allow the user to reset the password on the same page, there is no password reset token functionality, etc, etc.
How I exploit the vulnerability?
- First, I create two accounts on the application (Suppose [email protected] as the attacker’s account and [email protected] as the victim’s account)
- I went to the forgot password panel and enter attacker account information.
- I enter the attacker “Login ID” and “Email” and move to the next step which is “Security Questions”
- Now I again entered the attacker’s “Security Questions” and intercept the request.
- I found in the intercepted request, There are security question plus email address and username as well.
- I thought what if I change the email address and username with the victim’s email address and username?
- I change the email address and username with the victim’s email address and a username and forward the request.
- I reached to the password reset screen, I was totally blind if will update the password then which account’s password will be reset.
- I reset the password and booooom! Got an email on victim’s email address that your password has been reset.
What I actually have done, I enter the attacker’s username, email and security questions on the forgot password panel and before move on the password reset screen, I just change the email and username with victim’s email and username ![]()
Thanks a lot for reading protector47 writeup!

