Xencrypt
- PowerShell crypter v 1.0
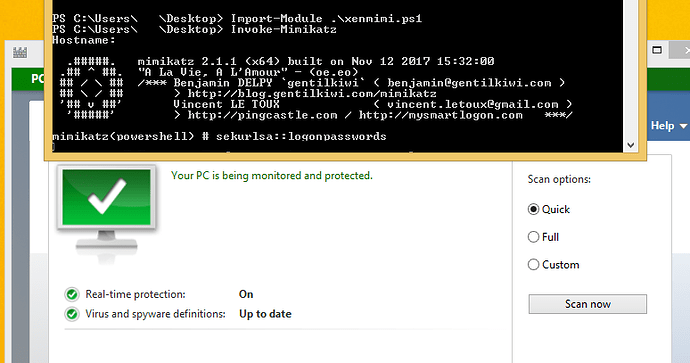
In action
Description
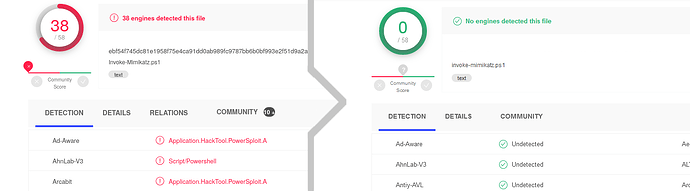
Tired of wasting lots of time obfuscating PowerShell scripts like invoke-mimikatz only to have them get detected anyway? Wouldn’t it be awesome if you could take any script and automatically and with almost no effort generate a near-infinite amount of variants in order to defeat signature-based antivirus detection mechanisms?
WELL, NOW YOU CAN! For the low low price of free! Xencrypt is a PowerShell crypter that uses AES encryption and Gzip/DEFLATE compression to with every invocation generate a completely unique yet functionally equivalent output script given any input script. It does this by compressing and encrypting the input script and storing this data as a payload in a new script which will unencrypt and decompress the payload before running it. In essence, it is to PowerShell what a PE crypter is.
Features
Xencrypt:
- Bypasses AMSI and all modern AVs in use on VirusTotal (as of writing)
- Compresses and encrypts powershell scripts
- Has a minimal and often even negative (thanks to the compression) overhead
- Randomizes variable names to further obfuscate the decrypter stub
- Randomizes encryption, compression and even the order that the statements appear in the code for maximum entropy!
- Super easy to modify to create your own crypter variant
- Supports recursive layering (crypter crypting the crypted output), tested up to 500 layers.
- Supports Import-Module as well as standard running as long as the input script also supported it
- GPLv3 – Free and open-source!
- All features in a single file so you can take it with you anywhere!
- Is despite all of the above not a silver bullet for every configuration – caveat emptor!