Wikipedia defines OSINT as follows:
“Open-source intelligence is data collected from publicly available sources to be used in an intelligence context. In the intelligence community, the term “open” refers to overt, publicly available sources. It is not related to open-source software or collective intelligence”

In this post, we are going to explore the TOP 20 Open-Source Intelligence (OSINT) tools you should know in 2020.
Let’s start exploring them:
Shodan
Shodan is a search engine that lets the user find specific types of computers (webcams, routers, servers, etc.) connected to the internet using a variety of filters. Some have also described it as a search engine of service banners, which are metadata that the server sends back to the client. This can be information about the server software, what options the service supports, a welcome message or anything else that the client can find out before interacting with the server.
You can use it by visiting the official website: www.shodan.io
Recon-NG

Open-source intelligence (OSINT) is data collected from publicly available sources to be used in an intelligence context. Recon-ng is a must-have OSINT tool. It was written in Python by lanmaster53 with many integrated modules and features. It contains 4 different categories of modules: Reconnaissance, Discovery, Reporting and experimental modules.

You can download it from here: https://github.com/lanmaster53/recon-ng
The Harvester

The Harvester is a tool for gathering email accounts, subdomain names, virtual hosts, open ports/ banners, and employee names from different public sources (search engines, pgp key servers). It is a really simple tool, but very effective for the early stages of a penetration test or just to know the visibility of your company on the Internet.

How I use theHarvester for Recon: https://www.youtube.com/watch?v=uHIvAqDTNLo
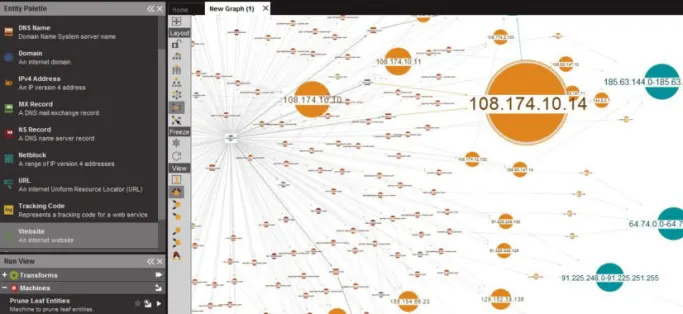
Maltego
Maltego is another OSINT tool. It is an interactive data mining tool that renders directed graphs for link analysis. The tool is used in online investigations for finding relationships between pieces of information from various sources located on the Internet. Maltego uses the idea of transforms to automate the process of querying different data sources. It was developed by Paterva. It provides you with transforms to help you gather information and visualize them. You can download the free edition from here: https://www.paterva.com/downloads.php
Exiftool

Sometimes files contain many juicy pieces of information. Many users are not aware of them. These pieces of information are represented as Metadata that can be extracted using many tools. One of the most popular tools to extract metadata from images is Exiftool. This tool is free and open-source. It was developed by Phil Harvey and it supports many operating systems including Windows, Mac OS and Linux

You can download it from here: https://exiftool.org
Global Terrorism Database

During many OSINT missions, you will be dealing with terrorism threats. Thus, it is essential to collect many pieces of information about terrorism online. One of the most used services is the “Global Terrorism Database”. The project is managed by the National Consortium for the Study of Terrorism and Responses to Terrorism (START) and it contains information about more than 190,000 terrorist attacks.
Its official website is: https://www.start.umd.edu/gtd/access/
OnionScan
The deep web, invisible web, or hidden web are parts of the World Wide Web whose contents are not indexed by standard web search engines for any reason. The opposite term to the deep web is the surface web, which is accessible to anyone using the Internet. Computer scientist Michael K. Bergman is credited with coining the term deep web in 2001 as a search indexing term. OnionScan is a free and open-source tool that is used in investigating the Dark web.
Its official website is: https://onionscan.org
DataSploit
Another powerful OSINT tool is DataSploit. This tool is a free and open-source. It gives you the ability to search for information about Companies, People, Phone Number, Bitcoin Addresses and so on. Once it collects the data it will generate reports as different formats such as HTML and JSON. It was written in python and It runs from the command line.
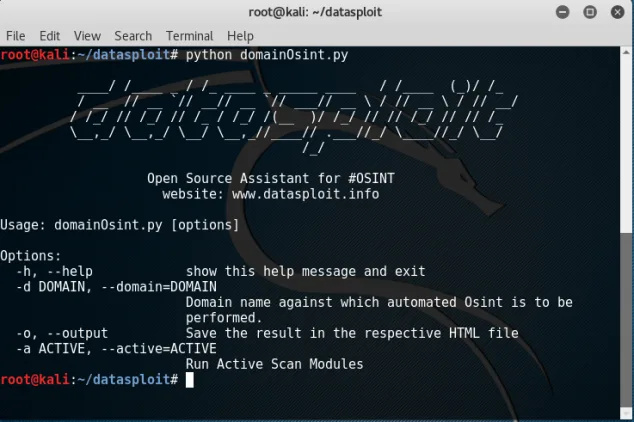
Its official Github repository is: https://github.com/DataSploit/datasploit
Openphish

Social engineering is a set of techniques (technical and nontechnical) used to get useful and sensitive information from others using psychological manipulation. Phishing is a Computer-based social engineering attack. To get information about active phishing links and URLs you can use “OpenPhish”. It provides a free phishing threat intelligence feed to track phishing URLs.
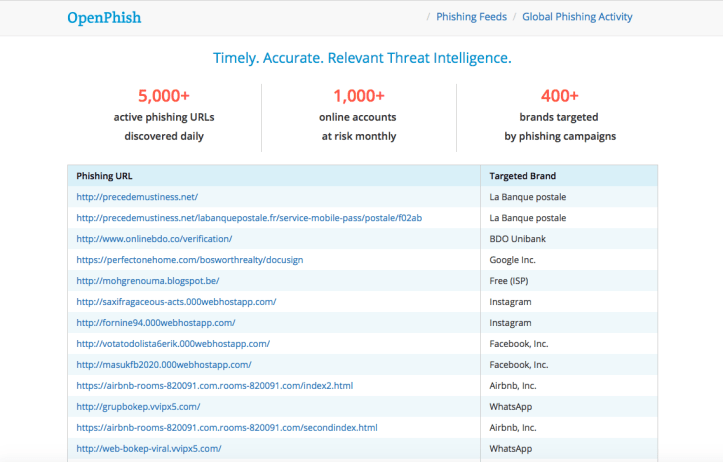
Its official website is: https://openphish.com
Malware Information Sharing Platform (MISP)

Malware Information Sharing Platform or simply MISP is an open-source threat sharing platform where analysts collaborate and share information about the latest threats between them. The project was developed by Christophe Vandeplas and it is under GPL v3 license.
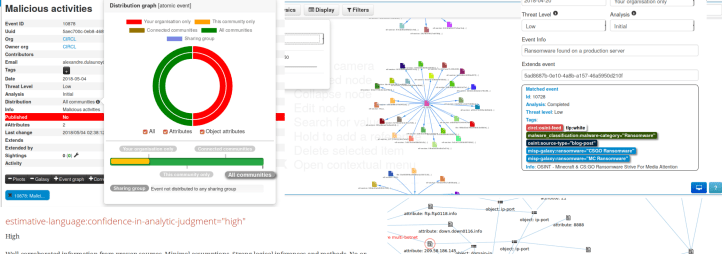
Its official website:https://www.misp-project.org
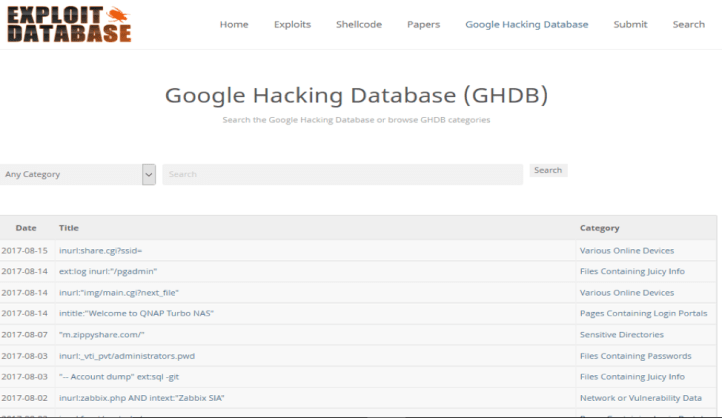
Google Dorks

If you are using Google as a search engine you can use what we call “Google Dorks”.A Google dork query, sometimes just referred to as a dork, is a search string that uses advanced search operators to find information that is not readily available on a website. Google dorking, also known as Google hacking, can return information that is difficult to locate through simple search queries.
For more information about Google dorks you can visit the Google Hacking Database: https://www.exploit-db.com/google-hacking-database/
Spiderfoot
![]()
Spiderfoot is a powerful OSINT tool with more than 200 modules to perform many operations including scanning, monitoring and analysis. It is free and open-source. It can perform TOR investigation too thanks to its built-in Tor integration. You can generate many different report formats including JSON, CSV and GEXF format
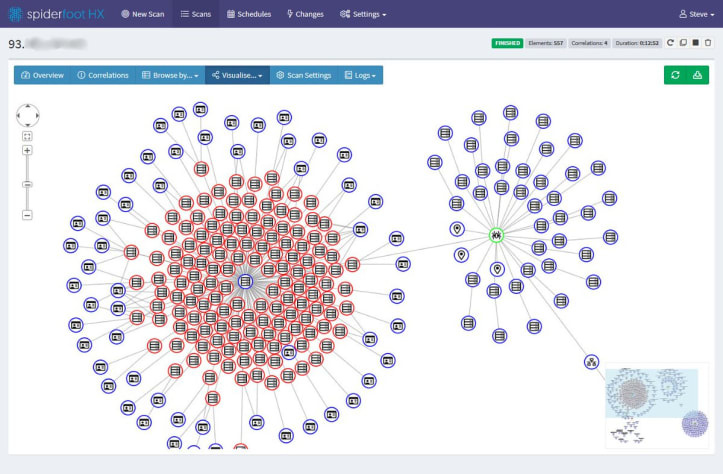
Its official website is: https://www.spiderfoot.net
Lampyre

Lampyre.io is an OSINT tool that gives you the ability to Obtain, visualize and analyze data in one place. You can import your own data to analyse it offline. It is widely used by Law enforcement, cybersecurity experts and financial analysts for many reasons including having updated data sources and the ability to use its Python API to customize your projects based on your needs and goals.
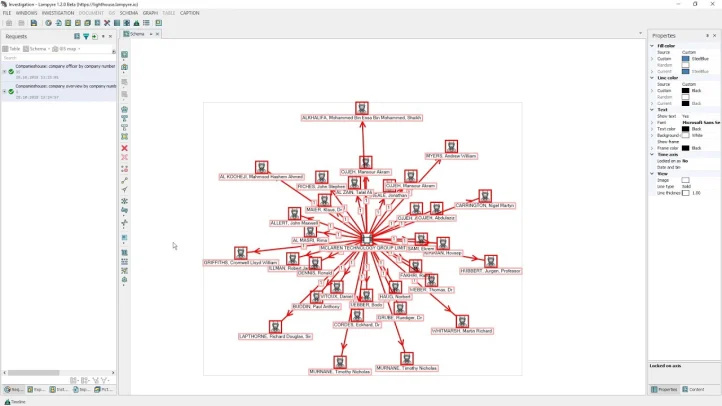
Its official website is: https://lampyre.io
Social Media
When performing open-source intelligence (OSINT), you usually try to find information about people from different publicly available social media platforms including: Facebook, Linkedin, Instagram and so on… To do so, you can use these powerful tools and websites:
An Instagram Open Source Intelligence Tool: https://onehack.us/t/instagram-osint-tool-gather-information-from-an-instagram-account/181305
Facebook Search tool: https://netbootcamp.org/facebook.html

Metapicz
Previously, we explored a metadata extraction tool called “Exiftool”. If you want a ready-to-use online tool you can simply use Metapicz. You just need to upload a picture and you will get all metadata of it and later you can analyse these pieces of information later.
Its official website is: http://metapicz.com/#landing
Carrot2

Carrot2 is an online and free tool that uses Carot2’s algorithm to search and organize results. The tool is free and it is under Apache v2 license. You can organize your search as folders, treemap or pie charts.
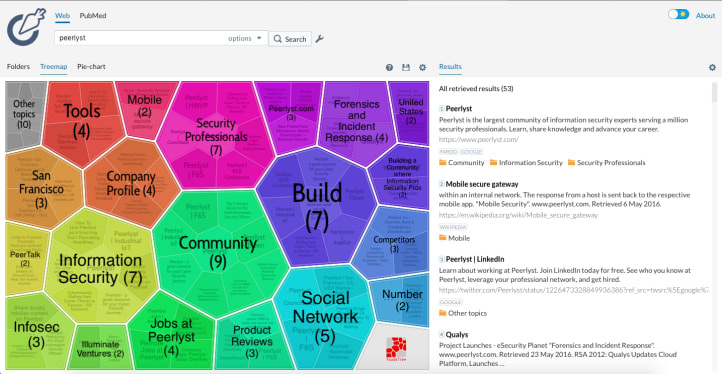
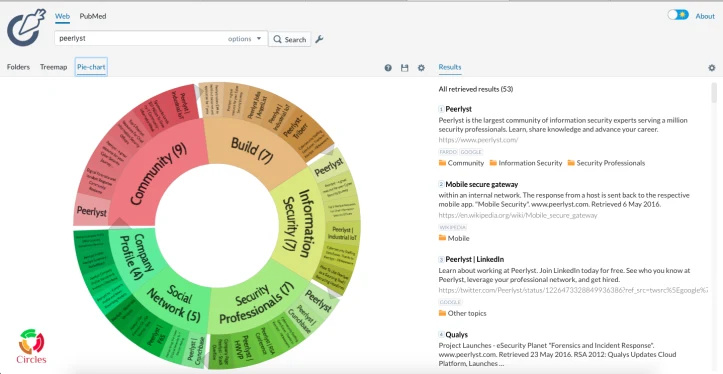
Its official website is: https://search.carrot2.org/#/web
Censys

We already explored Shodan in this list. Censys is another great online tool that helps you to collect technical information about a target. You can simply put an IP address and a domain and it will give you a list of important and helpful pieces of information including running services, geographic location, open ports and vulnerabilities and they are found.
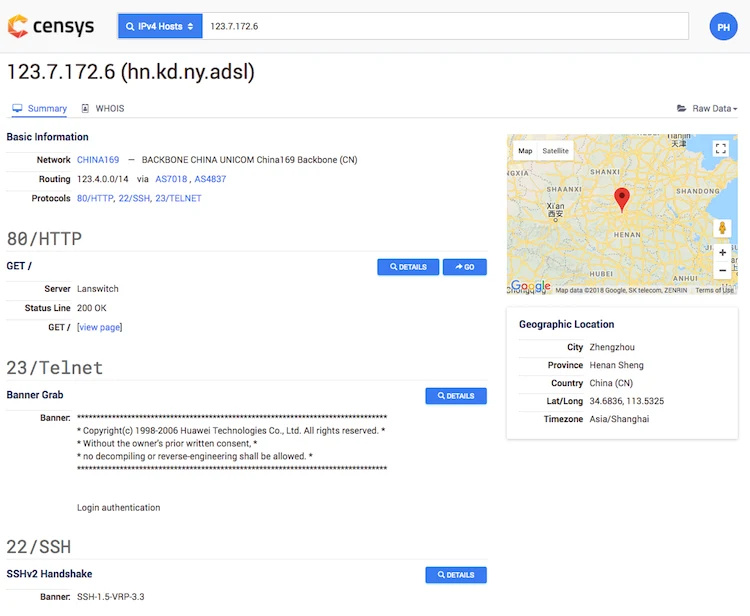
Its official website is: https://censys.io
DNS Dumpster
DNS Dumpster is a powerful tool maintained by HackerTarget.com. This free tool lets you discover hosts related to a specific domain. You can use it to visualize what attackers are seeing from the outside. Collected information can be presented as different formats including texts and visual maps. Also, it gives you the ability to build your own scripts thanks to its available API.
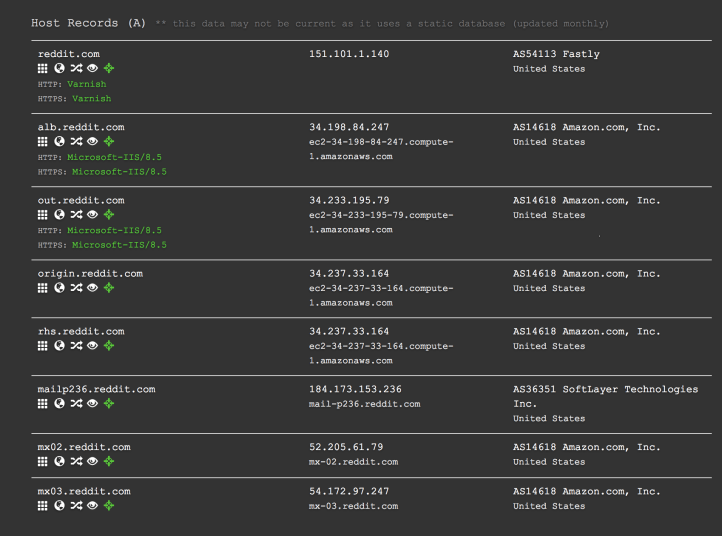
Its official website is: https://dnsdumpster.com
VirusTotal

To obtain many helpful pieces of information about a malicious file, we can use online virus scanners and search for its signature in search engines. VirusTotal is a free malware and URL online scanning service. It will deliver a result from more than 40 antivirus solutions. In other words, it gives you the ability to perform AV scanning using many AV solutions at the same time and later it delivers a detailed report about the suspicious file
FOCA

FOCA is the abbreviation of Fingerprinting Organizations with Collected Archives. Like its name indicates, this tool helps you collect metadata and information from documents. It can analyse many different file formats including Microsoft Office, Open Office, and PDF files.
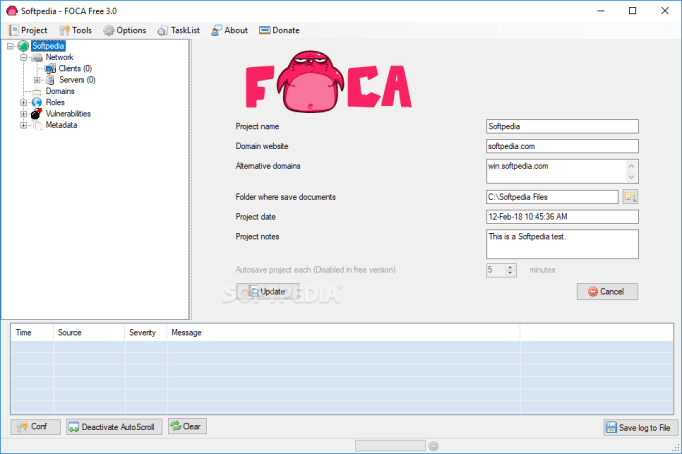
Its official Github repository is: https://github.com/ElevenPaths/FOCA
Bonus: Buscador VM (OSINT OS)
If you are looking for a ready to use the customized operating system you can simply use Buscador. This virtual machine contains a huge collection of OSINT tools and scripts to help you gather information about the targets. The VM was developed and maintained by https://inteltechniques.com
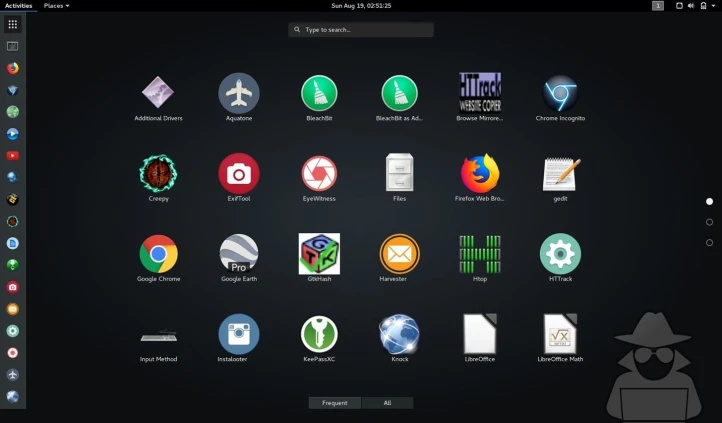
The VM can be downloaded from here: https://inteltechniques.com/buscador/
What are your favorite security tools?