Overview
Tails, an encrypted and anonymous OS that bundles widely used open-source privacy tools on a tiny device, is one of the most secure operating systems in the world. The Linux distribution rose to popularity when it was revealed Edward Snowden relied on Tails to secure his identity while sharing NSA secrets with journalists Glenn Greenwald and Laura Poitras. In the past half-decade, Tails has been embraced as an essential security suite by journalists, hackers, and IT workers.
Tails is a live system that aims to preserve your privacy and anonymity. It helps you to use the Internet anonymously and circumvent censorship almost anywhere you go and on any computer but leaving no trace unless you ask it to explicitly.
It is a complete operating system designed to be used from a USB stick or a DVD independently of the computer’s original operating system. It is Free Software and based on Debian GNU/Linux.
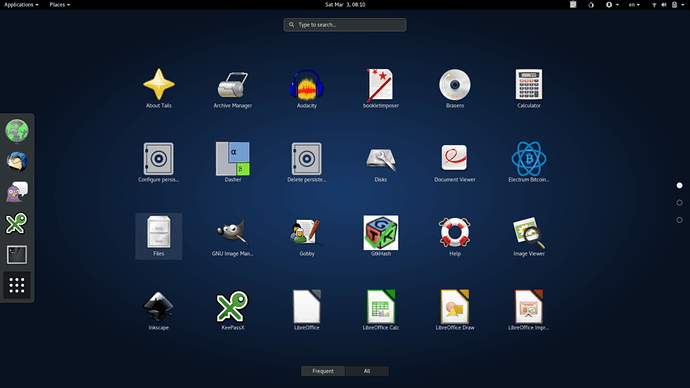
Tails comes with several built-in applications pre-configured with security in mind: web browser, instant messaging client, email client, office suite, image and sound editor, etc.
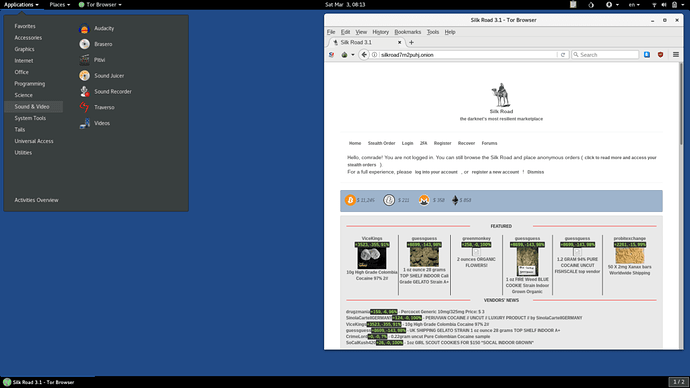
With Tails you can explore dark web (deep web) insecure way.
Online anonymity and censorship circumvention
Tor
Tails relies on the Tor anonymity network to protect your privacy online:
- all software is configured to connect to the Internet through Tor
- if an application tries to connect to the Internet directly, the connection is automatically blocked for security.
Tor is an open and distributed network that helps defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
Tor protects you by bouncing your communications around a network of relays run by volunteers all around the world: it prevents somebody watching your Internet connection from learning what sites you visit, and it prevents the sites you visit from learning your physical location.
Using Tor you can:
- be anonymous online by hiding your location,
- connect to services that would be censored otherwise;
- resist attacks that block the usage of Tor using circumvention tools such as bridges.
To learn more about Tor, see the official Tor website.
Use anywhere but leave no trace
Using Tails on a computer doesn’t alter or depend on the operating system installed on it. So you can use it in the same way on your computer, a friend’s computer, or one at your local library. After shutting down Tails, the computer will start again with its usual operating system.
Tails are configured with special care to not use the computer’s hard-disks, even if there is some swap space on them. The only storage space used by Tails is in RAM, which is automatically erased when the computer shuts down. So you won’t leave any trace on the computer either of the Tails system itself or what you used it for. That’s why we call Tails “amnesic”.
This allows you to work with sensitive documents on any computer and protects you from data recovery after shutdown. Of course, you can still explicitly save specific documents to another USB stick or external hard-disk and take them away for future use.
State of the art cryptographic tools
Tails also come with a selection of tools to protect your data using strong encryption:
- Encrypt your USB sticks or external hard-disks using LUKS, the Linux standard for disk encryption.
- Automatically use HTTPS to encrypt all your communications to a number of major websites using HTTPS Everywhere, a Firefox extension developed by the Electronic Frontier Foundation.
- Encrypt and sign your emails and documents using the de facto standard OpenPGP either from Tails email client, text editor or file browser.
- Protect your instant messaging conversations using OTR, a cryptographic tool that provides encryption, authentication, and deniability.
- Securely delete your files and clean your disk space using Nautilus Wipe.
Read more about those tools in the documentation.
Features and included software
- Included software
- Networking
- Desktop edition
- Encryption and privacy
- Additional software
- Additional features
- Multilingual support
Tails is based on Debian 10 (Buster).
Installation
To install Tails on a new USB stick
Follow our installation instructions: