When working with Windows File Explorer on the server as a local administrator, you often have to open system directories, user profiles or edit protected system files. When trying to open such directory/file in Windows Explorer in the current context, the UAC warning appears prompting to grant access and elevate privileges.
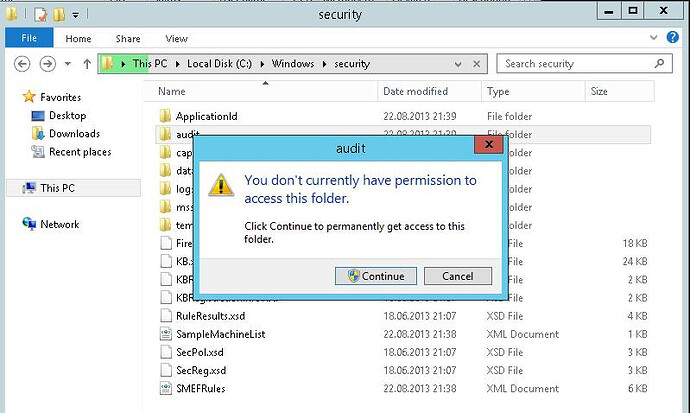
What it looks like: let’s try to open a system folder C:\Windows\security\audit in Windows Explorer. User Account Control window appears to warn that you cannot access this folder ( You don’t currently have permission to access this folder ). But you can get access by clicking Continue.
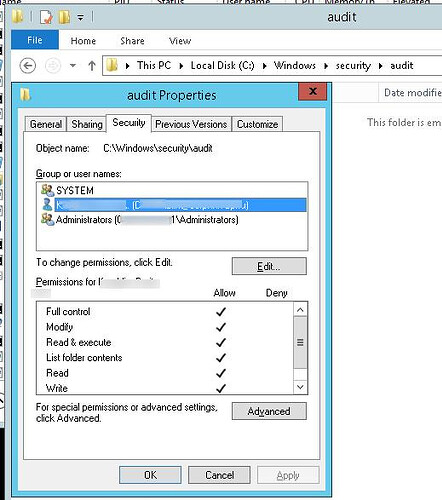
It’s ok, but if you do it, your account is explicitly written in the NTFS permissions for the folder. But all you want to do is to look through the contents of the folder, and not to change its ACL!
Naturally, when you often work with system files, this UAC warning becomes irritating. Since we didn’t want to disable UAC, we had to find our own way to start elevated Windows Explorer process (Exploler.exe)
Note . Windows Explorer process starts when a user logs into the system with the standard user access token, works in the background and is responsible for showing desktop. You cannot elevate privileges for Explorer with the standard means, and also you won’t be able to run the second process as admin.
- Run cmd.exe as administrator
- Run the command:
tskill explorer & explorer
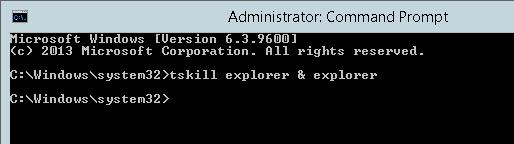
This command will terminate the current explorer.exe process for this user and start a new one that will inherit the elevated access token cmd.exe is run with.
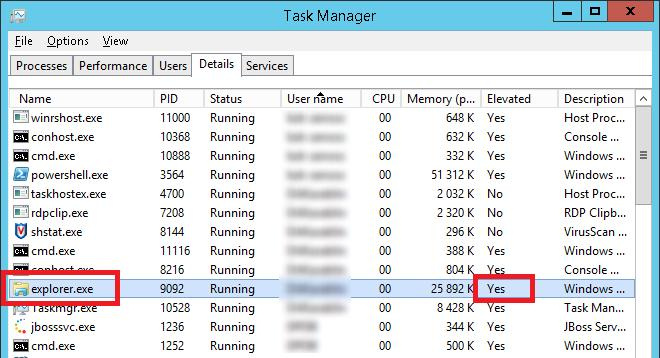
You can make sure that Windows Explorer is running elevated in the Task Manager . Start it, and go to the Details tab. Right-click any column, click Select columns and enable Elevated column to be displayed. As you can see, explorer.exe is now having attribute Elevated=Yes .
After that Explorer will be able to open any system folder without a UAC warning, and all child processes run from Windows Explorer will run elevated. For example, it is convenient when you need to edit hosts file (c:windowssystem32driversetc): you can open it right from Explorer using Notepad, with no need to start a separate notepad.exe process as administrator.
To make it partially automatic, you can create a .bat file containing this command on the desktop and right-click to run it as an administrator to elevate privileges.