The list was shared by the operator of a DDoS booter service.
A hacker has published this week a massive list of Telnet credentials for more than 515,000 servers, home routers, and IoT (Internet of Things) “smart” devices.
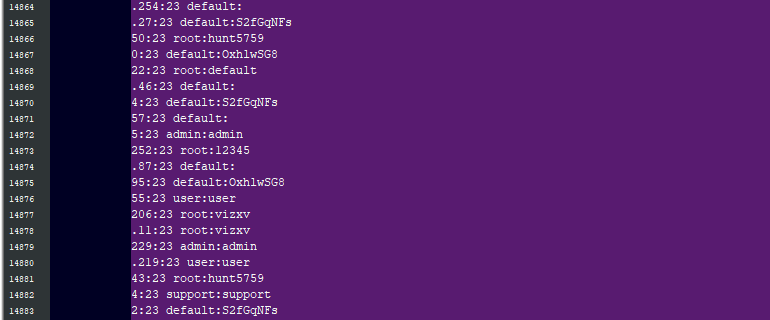
The list, which was published on a popular hacking forum, includes each device’s IP address, along with a username and password for the Telnet service, a remote access protocol that can be used to control devices over the internet.
According to experts to who we spoke this week, and a statement from the leaker himself, the list was compiled by scanning the entire internet for devices that were exposing their Telnet port. The hacker than tried using (1) factory-set default usernames and passwords, or (2) custom, but easy-to-guess password combinations.
These types of lists – called “bot lists” – are a common component of an IoT botnet operation. Hackers scan the internet to build bot lists, and then use them to connect to the devices and install malware.
These lists are usually kept private, although some have leaked online in the past, such as a list of 33,000 home router Telnet credentials that leaked in August 2017. To our knowledge, this marks the biggest leak of Telnet passwords known to date.
DATA LEAKED BY A DDOS SERVICE OPERATOR
As we understands, the list was published online by the maintainer of a DDoS-for-hire (DDoS booter) service.
When asked why he published such a massive list of “bots,” the leaker said he upgraded his DDoS service from working on top of IoT botnets to a new model that relies on renting high-output servers from cloud service providers.
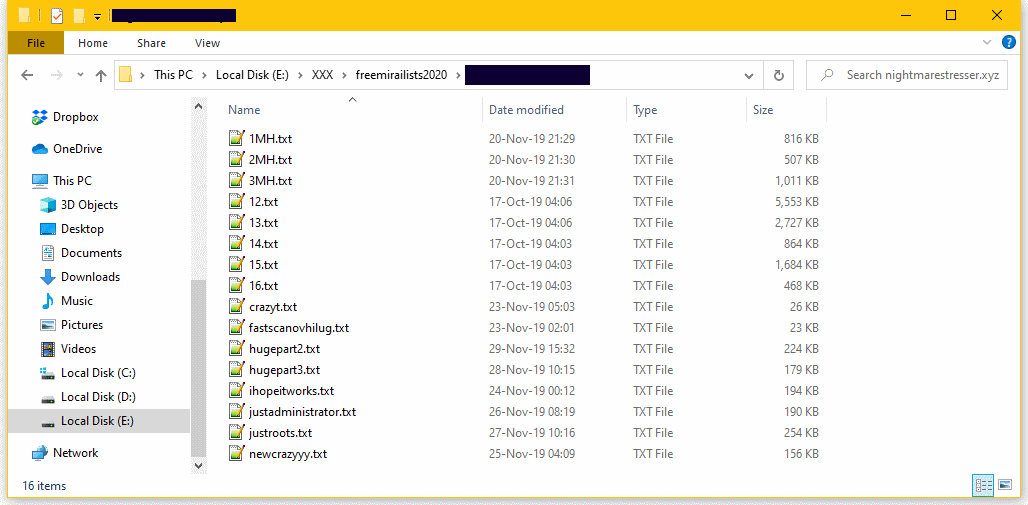
All the lists the hacker leaked are dated October-November 2019. Some of these devices might now run on a different IP address, or use different login credentials.
1Hack did not use any of the username and password combos to access any of the devices, as this would be illegal – hence we are unable to tell home many of these credentials are still valid.
Using IoT search engines like BinaryEdge and Shodan, we identified devices all over the world. Some devices were located on the networks of known internet service providers (indicating they were either home router or IoT devices), but other devices were located on the networks of major cloud service providers.
DANGER REMAINS
An IoT security expert (who wanted to remain anonymous) told us that even if some entries on the list are not valid anymore because devices might have changed their IP address or passwords, the lists remain incredibly useful for a skilled attacker.
Misconfigured devices are not evenly spread out across the internet, but they’re usually clustered on the network of one single ISP due to the ISP’s staff misconfiguring the devices when deploying them to their respective customerbases.
An attacker could use the IP addresses included in the lists, determine the service provider, and then re-scan the ISP’s network to update the list with the latest IP addresses.
We shared the credentials list with trusted and vetted security researchers who volunteered to contact and notify ISPs and server owners.
Source: zdnet






 !
!