Hack microsoft using microsoft signed binaries - Pierre-alexandre braeken
This document is the supporting white paper for the presentation hack microsoft using microsoft Signed binaries at black hat asia 2017 in singapore.
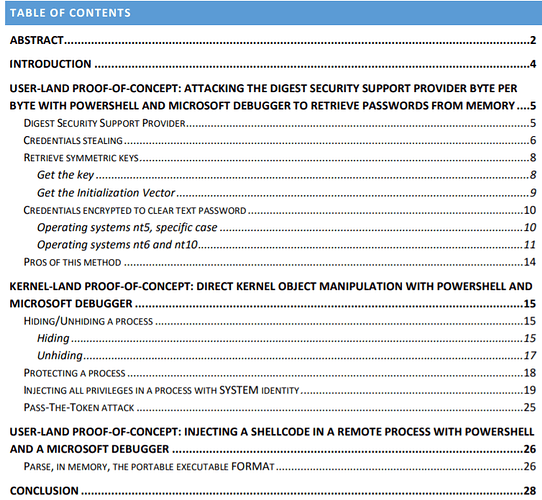
Abstract
In Windows, the user-land and kernel-land memory can be accessed and modified using
Windows APIs. Our proof-of-concept will show how to access Windows memory without using
complex programming language and without calling Windows APIs.
The signed debugging tools for Windows provided by Microsoft will help us abuse the Windows
operating system due to them being trusted by default because they are signed with
sha1/sha256 Microsoft certificates.
We chose PowerShell for its prevalence in corporate environment instead of using a basic script
language (e.g.: Windows batch). In addition, the method we will show doesn’t use Windows API
reflection thus hindering substantially its detection and mitigation.
Presently, WCE and Mimikatz already reveal passwords from Windows memory. Nevertheless,
there is no other tool using the approach of PowerShell piloting a Microsoft Windows debugger
to achieve this goal.
Furthermore, we will show different techniques to manipulate the memory in user-land and
kernel-land contexts using this concept.
How “deep” can we dig into the Windows memory just by using a debugger?
KEYWORDS: debugger attack, offensive PowerShell automation, kernel security, process
injection, DKOM